Hacker II: The Doomsday Papers
| Hacker II: The Doomsday Papers | |
|---|---|
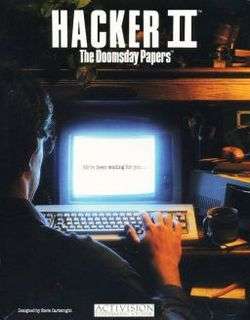 Cover art | |
| Developer(s) | Activision |
| Publisher(s) | Activision |
| Designer(s) | Steve Cartwright[1] |
| Platform(s) | Amiga, Amstrad CPC, Apple II, Apple IIGS, Atari ST, C64, IBM PC, Macintosh, ZX Spectrum |
| Release | 1986 |
| Genre(s) | Puzzle/Strategy |
| Mode(s) | Single player |
Hacker II: The Doomsday Papers is computer game written by Steve Cartwright and published by Activision in 1986.[1] It is the sequel to the 1985 game, Hacker. Hacker II was released for the Amiga, Apple II, Apple IIGS, Amstrad CPC, Atari ST, Commodore 64, IBM PC, Macintosh, and ZX Spectrum.
Plot
Hacker II is more difficult and involved than the first game. In Hacker II, the player is actually recruited based upon his (assumed) success with the activities in the original game. Once again, they are tasked with controlling a robot, this time to infiltrate a secure facility in order to retrieve documents known only as "The Doomsday Papers" from a well guarded vault to ensure the security of the United States.
Eventually, as they escape with the papers, the player is confronted by agents of the United States who reveal that he or she have actually been working for a former Magma employee, who wanted the papers in revenge for what had happened to the company the player had presumably exposed in the first game. The building that the player had unwittingly broken into was a government facility. The player then has to go back into the facility as part of a gambit to expose the Magma agent, avoiding the same security that had threatened the player before.
Gameplay
Gameplay is considerably changed from the previous game and the packaging is notable for including a "manual" describing the function of a four way monitor system provided to the player. It is hooked into the camera security network of the facility the player is asked to infiltrate. A handful of robots are available, hidden in the facility, in case some are lost. By using the camera system and in-game map that helps track guard patrols and the location of the robots, the player must explore the one floor facility and find the codes needed to open the vault and escape with the papers.
Discovery by the guards must be avoided at all costs because once alerted, they will call in a huge machine that resembles a large plate hung from what looks like a metal frame on wheels. This machine pursues the player's defenseless robot and attempt to crush it with the plate. The player can try and avoid the drone, although it is relentless in its pursuit and is much faster than the player's robot. If all the player's robots are destroyed, the game is over.
The game also featured escalating problems as part of the player's interface begins to fail, the ingame map starts to lose progress of the player's robot, monitored security cameras, the guard and eventually the map itself as the player defeated the system, eventually to get into the vault the player may well be forced to control the robot blindly relying on maps that should have been made by the player.
There are no saves available in the game as in the first title.
Reception
Compute! described Hacker II as not having an original plot and criticized the inability to save, but favorably reported on the game's graphics, detail, and user interface. The magazine stated that it had "some of the most exciting and harrowing scenarios you'll find in a computer game" and advised, "I do not recommend it to anyone with a weak heart".[2] Computer Gaming World praised Hacker II's graphics and design on the Atari ST, and stated that the game more accurately depicted system cracking than Hacker, but cautioned that its difficulty and scale would not appeal to everyone.[3]
References
- 1 2 "The Giant List of Classic Game Programmers". dadgum.com.
- ↑ Randall, Neil (November 1986). "Hacker II: The Doomsday Papers". Compute!. p. 67. Retrieved 9 November 2013.
- ↑ Williams, Gregg (December 1986). "Hacker II" (PDF). Computer Gaming World. No. 33. p. 18. Retrieved 23 April 2016.
External links
- Hacker II: The Doomsday Papers at Lemon 64
- Hacker II: The Doomsday Papers at SpectrumComputing.co.uk
- The MS-DOS version of Hacker II: The Doomsday Papers can be played for free in the browser at the Internet Archive