Bitcoin network

The bitcoin network is a peer-to-peer payment network that operates on a cryptographic protocol. Users send and receive bitcoins, the units of currency, by broadcasting digitally signed messages to the network using bitcoin wallet software. Transactions are recorded into a distributed, replicated public database known as the blockchain, with consensus achieved by a proof-of-work system called "mining". The protocol was designed in 2008 and released in 2009 as open source software by "Satoshi Nakamoto", the name or pseudonym of the original developer/developer group.
The network requires minimal structure to share transactions. An ad hoc decentralized network of volunteers is sufficient. Messages are broadcast on a best effort basis, and nodes can leave and rejoin the network at will. Upon reconnection, a node downloads and verifies new blocks from other nodes to complete its local copy of the blockchain.[1][2]
Transactions
A bitcoin is defined by a sequence of digitally signed transactions that began with the bitcoin's creation, as a block reward. The owner of a bitcoin transfers it by digitally signing it over to the next owner using a bitcoin transaction, much like endorsing a traditional bank check. A payee can examine each previous transaction to verify the chain of ownership. Unlike traditional check endorsements, bitcoin transactions are irreversible, which eliminates risk of chargeback fraud.[3]
Although it is possible to handle bitcoins individually, it would be unwieldy to require a separate transaction for every bitcoin in a transaction. Transactions are therefore allowed to contain multiple inputs and outputs,[4] allowing bitcoins to be split and combined. Common transactions will have either a single input from a larger previous transaction or multiple inputs combining smaller amounts, and one or two outputs: one for the payment, and one returning the change, if any, to the sender. Any difference between the total input and output amounts of a transaction goes to miners as a transaction fee.[1]
Mining


To form a distributed timestamp server as a peer-to-peer network, bitcoin uses a proof-of-work system.[2] The work in this system is what is often referred to as bitcoin mining. The signature is discovered rather than provided by knowledge.[5] This process is energy intensive.[6] Electricity can consume more than 90% of operating costs for miners.[7] A data center in China, planned mostly for bitcoin mining, is expected to require up to 135 MW of power.[8]
The rule of requiring a proof-of-work to provide the signature for the blockchain was Satoshi Nakamoto's key innovation.[5] The mining process involves identifying a block that when hashed twice with SHA-256, yields a number smaller than the given difficulty target. While the average work required increases in inverse proportion to the difficulty target, a hash can always be verified by executing a single round of double SHA-256.
For the bitcoin timestamp network, a valid "proof-of-work" is found by incrementing a nonce until a value is found that gives the block's hash the required number of leading zero bits. Once the hashing has produced a valid result, the block cannot be changed without redoing the work. As later blocks are chained after it, the work to change the block would include redoing the work for each subsequent block.
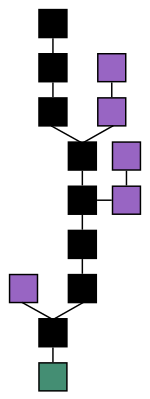
Majority consensus in bitcoin is represented by the longest chain, which required the greatest amount of effort to produce. If a majority of computing power is controlled by honest nodes, the honest chain will grow fastest and outpace any competing chains. To modify a past block, an attacker would have to redo the proof-of-work of that block and all blocks after it and then surpass the work of the honest nodes. The probability of a slower attacker catching up diminishes exponentially as subsequent blocks are added.[2]

To compensate for increasing hardware speed and varying interest in running nodes over time, the difficulty of finding a valid hash is adjusted roughly every two weeks. If blocks are generated too quickly, the difficulty increases and more hashes are required to make a block and to generate new bitcoins.[2]
Difficulty
Bitcoin mining is a competitive endeavor. An "arms race" has been observed through the various hashing technologies that have been used to mine bitcoins: basic CPUs, high-end GPUs common in many gaming computers, FPGAs and ASICs all have been used, each reducing the profitability of the less-specialized technology. Bitcoin-specific ASICs are now available.[9] As bitcoins become more difficult to mine, computer hardware manufacturing companies have seen an increase in sales of high-end products.[10]
Computing power is often bundled together or "pooled" to reduce variance in miner income. Individual mining rigs often have to wait for long periods to confirm a block of transactions and receive payment. In a pool, all participating miners get paid every time a participating server solves a block. This payment is proportional to the amount of work an individual miner contributed to help find that block.[11]
Bitcoin data centers prefer to keep a low profile, are dispersed around the world and tend to cluster around the availability of cheap electricity.[7]
Energy consumption

In 2013, Mark Gimein estimated electricity use to be about 40.9 megawatts (982 megawatt-hours a day).[12] In 2014, Hass McCook estimated 80.7 megawatts (80,666 kW).[13] As of 2015, The Economist estimated that even if all miners used modern facilities, the combined electricity consumption would be 166.7 megawatts (1.46 terawatt-hours per year).[14]
Journalist Matt O'Brien opined that it is not obvious whether bitcoin is lowering transaction costs, since the costs are transformed into pollution costs, which he characterizes as "environmental spillovers on everyone else, or what economists call negative externalities."[15]
To lower the costs, bitcoin miners have set up in places like Iceland where geothermal energy is cheap and cooling Arctic air is free.[15] Chinese bitcoin miners are known to use hydroelectric power in Tibet to reduce electricity costs.[16]
Process


A rough overview of the process to mine bitcoins is:[2]
- New transactions are broadcast to all nodes.
- Each miner node collects new transactions into a block.
- Each miner node works on finding a proof-of-work code for its block.
- When a node finds a proof-of-work, it broadcasts the block to all nodes.
- Receiving nodes validate the transactions it holds and accept only if all are valid.
- Nodes express their acceptance by moving to work on the next block, incorporating the hash of the accepted block.
Mined bitcoins
By convention, the first transaction in a block is a special transaction that produces new bitcoins owned by the creator of the block. This is the incentive for nodes to support the network.[1] It provides the way to move new bitcoins into circulation. The reward for mining halves every 210,000 blocks. It started at 50 bitcoin, dropped to 25 in late 2012 and to 12.5 bitcoin in 2016.[17] This halving process is programmed to continue for 64 times before new coin creation ceases.[17]
Security
Various potential attacks on the bitcoin network and its use as a payment system, real or theoretical, have been considered. The bitcoin protocol includes several features that protect it against some of those attacks, such as unauthorized spending, double spending, forging bitcoins, and tampering with the blockchain. Other attacks, such as theft of private keys, require due care by users.[18][19][20][21][22][23][24]
Unauthorized spending
Unauthorized spending is mitigated by bitcoin's implementation of public-private key cryptography. For example; when Alice sends a bitcoin to Bob, Bob becomes the new owner of the bitcoin. Eve observing the transaction might want to spend the bitcoin Bob just received, but she cannot sign the transaction without the knowledge of Bob's private key.[19]
Double spending
A specific problem that an internet payment system must solve is double-spending, whereby a user pays the same coin to two or more different recipients. An example of such a problem would be if Eve sent a bitcoin to Alice and later sent the same bitcoin to Bob. The bitcoin network guards against double-spending by recording all bitcoin transfers in a ledger (the blockchain) that is visible to all users, and ensuring for all transferred bitcoins that they haven't been previously spent.[19]:4
Race attack
If Eve offers to pay Alice a bitcoin in exchange for goods and signs a corresponding transaction, it is still possible that she also creates a different transaction at the same time sending the same bitcoin to Bob. By the rules, the network accepts only one of the transactions. This is called a race attack, since there is a race which transaction will be accepted first. Alice can reduce the risk of race attack stipulating that she will not deliver the goods until Eve's payment to Alice appears in the blockchain.[20]
A variant race attack (which has been called a Finney attack by reference to Hal Finney) requires the participation of a miner. Instead of sending both payment requests (to pay Bob and Alice with the same coins) to the network, Eve issues only Alice's payment request to the network, while the accomplice tries to mine a block that includes the payment to Bob instead of Alice. There is a positive probability that the rogue miner will succeed before the network, in which case the payment to Alice will be rejected. As with the plain race attack, Alice can reduce the risk of a Finney attack by waiting for the payment to be included in the blockchain.[21]
History modification
Each block that is added to the blockchain, starting with the block containing a given transaction, is called a confirmation of that transaction. Ideally, merchants and services that receive payment in bitcoin should wait for at least one confirmation to be distributed over the network, before assuming that the payment was done. The more confirmations that the merchant waits for, the more difficult it is for an attacker to successfully reverse the transaction in a blockchain—unless the attacker controls more than half the total network power, in which case it is called a 51% attack.[22]
Deanonymisation of clients
Deanonymisation is a strategy in data mining in which anonymous data is cross-referenced with other sources of data to re-identify the anonymous data source. Along with transaction graph analysis, which may reveal connections between bitcoin addresses (pseudonyms),[18][23] there is a possible attack[24] which links a user's pseudonym to its IP address. If the peer is using Tor, the attack includes a method to separate the peer from the Tor network, forcing them to use their real IP address for any further transactions. The attack makes use of bitcoin mechanisms of relaying peer addresses and anti-DoS protection. The cost of the attack on the full bitcoin network is under €1500 per month.[24]
Payment verification
Each miner can choose which transactions are included in or exempted from a block.[25] A greater number of transactions in a block does not equate to greater computational power required to solve that block.[25]
Upon receiving a new transaction a node must validate it: in particular, verify that none of the transaction's inputs have been previously spent. To carry out that check the node needs to access the blockchain. Any user who does not trust his network neighbors, should keep a full local copy of the blockchain, so that any input can be verified.
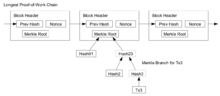
As noted in Nakamoto's whitepaper, it is possible to verify bitcoin payments without running a full network node (simplified payment verification, SPV). A user only needs a copy of the block headers of the longest chain, which are available by querying network nodes until it is apparent that the longest chain has been obtained. Then, get the Merkle branch linking the transaction to its block. Linking the transaction to a place in the chain demonstrates that a network node has accepted it, and blocks added after it further establish the confirmation.[1]
Data in the blockchain
While it is possible to store any digital file in the blockchain, the larger the transaction size, the larger any associated fees become.[26] Various items have been embedded, including URLs to child pornography, an ASCII art image of Ben Bernanke, material from the Wikileaks cables, prayers from bitcoin miners, and the original bitcoin whitepaper.[27]
Criminal activity
The use of bitcoin by criminals has attracted the attention of financial regulators, legislative bodies, law enforcement, and the media.[28] The FBI prepared an intelligence assessment,[29] the SEC has issued a pointed warning about investment schemes using virtual currencies,[28] and the U.S. Senate held a hearing on virtual currencies in November 2013.[30]
Several news outlets have asserted that the popularity of bitcoins hinges on the ability to use them to purchase illegal goods.[31][32] In 2014, researchers at the University of Kentucky found "robust evidence that computer programming enthusiasts and illegal activity drive interest in bitcoin, and find limited or no support for political and investment motives."[33]
Black markets
A CMU researcher estimated that in 2012, 4.5% to 9% of all transactions on all exchanges in the world were for drug trades on a single dark web drugs market, Silk Road.[34] Child pornography,[35] murder-for-hire services,[36] and weapons[37] are also allegedly available on black market sites that sell in bitcoin. Due to the anonymous nature and the lack of central control on these markets, it is hard to know whether the services are real or just trying to take the bitcoins.[38]
Several deep web black markets have been shut by authorities. In October 2013 Silk Road was shut down by U.S. law enforcement[39][40][41] leading to a short-term decrease in the value of bitcoin.[42] In 2015, the founder of the site was sentenced to life in prison.[43] Alternative sites were soon available, and in early 2014 the Australian Broadcasting Corporation reported that the closure of Silk Road had little impact on the number of Australians selling drugs online, which had actually increased.[44] In early 2014, Dutch authorities closed Utopia, an online illegal goods market, and seized 900 bitcoins.[45] In late 2014, a joint police operation saw European and American authorities seize bitcoins and close 400 deep web sites including the illicit goods market Silk Road 2.0.[46] Law enforcement activity has resulted in several convictions. In December 2014, Charlie Shrem was sentenced to two years in prison for indirectly helping to send $1 million to the Silk Road drugs site,[47] and in February 2015, its founder, Ross Ulbricht, was convicted on drugs charges and faces a life sentence.[48]
Some black market sites may seek to steal bitcoins from customers. The bitcoin community branded one site, Sheep Marketplace, as a scam when it prevented withdrawals and shut down after an alleged bitcoins theft.[49] In a separate case, escrow accounts with bitcoins belonging to patrons of a different black market were hacked in early 2014.[50]
According to the Internet Watch Foundation, a UK-based charity, bitcoin is used to purchase child pornography, and almost 200 such websites accept it as payment. Bitcoin isn't the sole way to purchase child pornography online, as Troels Oertling, head of the cybercrime unit at Europol, states, "Ukash and Paysafecard... have [also] been used to pay for such material." However, the Internet Watch Foundation lists around 30 sites that exclusively accept bitcoins.[35] Some of these sites have shut down, such as a deep web crowdfunding website that aimed to fund the creation of new child porn.[51] Furthermore, hyperlinks to child porn websites have been added to the blockchain as arbitrary data can be included when a transaction is made.[52][53]
Malware
Malware stealing
Some malware can steal private keys for bitcoin wallets allowing the bitcoins themselves to be stolen. The most common type searches computers for cryptocurrency wallets to upload to a remote server where they can be cracked and their coins stolen.[54] Many of these also log keystrokes to record passwords, often avoiding the need to crack the keys.[54] A different approach detects when a bitcoin address is copied to a clipboard and quickly replaces it with a different address, tricking people into sending bitcoins to the wrong address.[55] This method is effective because bitcoin transactions are irreversible.[56]:57
One virus, spread through the Pony botnet, was reported in February 2014 to have stolen up to $220,000 in cryptocurrencies including bitcoins from 85 wallets.[57] Security company Trustwave, which tracked the malware, reports that its latest version was able to steal 30 types of digital currency.[58]
A type of Mac malware active in August 2013, Bitvanity posed as a vanity wallet address generator and stole addresses and private keys from other bitcoin client software.[59] A different trojan for macOS, called CoinThief was reported in February 2014 to be responsible for multiple bitcoin thefts.[59] The software was hidden in versions of some cryptocurrency apps on Download.com and MacUpdate.[59]
Ransomware
Some ransomware demand payment in bitcoin. One program called CryptoLocker, typically spread through legitimate-looking email attachments, encrypts the hard drive of an infected computer, then displays a countdown timer and demands a ransom, usually two bitcoins, to decrypt it.[60] Massachusetts police said they paid a 2 bitcoin ransom in November 2013, worth more than $1,300 at the time, to decrypt one of their hard drives.[61] Linkup, a combination ransomware and bitcoin mining program that surfaced in February 2014, disables internet access and demands credit card information to restore it, while secretly mining bitcoins.[60] Bitcoin is currently being used as the ransom medium of choice in the WannaCry ransomware hack hitting many buildings in Asia and Europe.[62]
Unauthorized mining
In June 2011, Symantec warned about the possibility that botnets could mine covertly for bitcoins.[63] Malware used the parallel processing capabilities of GPUs built into many modern video cards.[64] Although the average PC with an integrated graphics processor is virtually useless for bitcoin mining, tens of thousands of PCs laden with mining malware could produce some results.[65]
In mid-August 2011, bitcoin mining botnets were detected,[66] and less than three months later, bitcoin mining trojans had infected Mac OS X.[67]
In April 2013, electronic sports organization E-Sports Entertainment was accused of hijacking 14,000 computers to mine bitcoins; the company later settled the case with the State of New Jersey.[68]
German police arrested two people in December 2013 who customized existing botnet software to perform bitcoin mining, which police said had been used to mine at least $950,000 worth of bitcoins.[69]
For four days in December 2013 and January 2014, Yahoo! Europe hosted an ad containing bitcoin mining malware that infected an estimated two million computers.[70] The software, called Sefnit, was first detected in mid-2013 and has been bundled with many software packages. Microsoft has been removing the malware through its Microsoft Security Essentials and other security software.[71]
Several reports of employees or students using university or research computers to mine bitcoins have been published.[72]
Money laundering
Bitcoins may not be ideal for money laundering, because all transactions are public.[73] Authorities, including the European Banking Authority[74] the FBI,[29] and the Financial Action Task Force of the G7[75] have expressed concerns that bitcoin may be used for money laundering. In early 2014, an operator of a U.S. bitcoin exchange, Charlie Shrem, was arrested for money laundering.[76] Subsequently, he was sentenced to two years in prison for "aiding and abetting an unlicensed money transmitting business".[47] A report by UK's Treasury and Home Office named "UK national risk assessment of money laundering and terrorist financing" (2015 October) found that, of the twelve methods examined in the report, bitcoin carries the lowest risk of being used for money laundering, with the most common money laundering method being the banks.[77]
Ponzi scheme
In a Ponzi scheme that utilized bitcoins, The Bitcoin Savings and Trust promised investors up to 7 percent weekly interest, and raised at least 700,000 bitcoins from 2011 to 2012.[78] In July 2013 the U.S. Securities and Exchange Commission charged the company and its founder in 2013 "with defrauding investors in a Ponzi scheme involving bitcoin".[78] In September 2014 the judge fined Bitcoin Savings & Trust and its owner $40 million for operating a bitcoin Ponzi scheme.[79]
Theft
There have been many cases of bitcoin theft.[80] One way this is accomplished involves a third party accessing the private key to a victim's bitcoin address,[81] or of an online wallet.[82] If the private key is stolen, all the bitcoins from the compromised address can be transferred. In that case, the network does not have any provisions to identify the thief, block further transactions of those stolen bitcoins, or return them to the legitimate owner.[83]
Theft also occurs at sites where bitcoins are used to purchase illicit goods. In late November 2013, an estimated $100 million in bitcoins were allegedly stolen from the online illicit goods marketplace Sheep Marketplace, which immediately closed.[84] Users tracked the coins as they were processed and converted to cash, but no funds were recovered and no culprits identified.[84] A different black market, Silk Road 2, stated that during a February 2014 hack, bitcoins valued at $2.7 million were taken from escrow accounts.[50]
Sites where users exchange bitcoins for cash or store them in "wallets" are also targets for theft. Inputs.io, an Australian wallet service, was hacked twice in October 2013 and lost more than $1 million in bitcoins.[85] In late February 2014 Mt. Gox, one of the largest virtual currency exchanges, filed for bankruptcy in Tokyo amid reports that bitcoins worth $350 million had been stolen.[86] Flexcoin, a bitcoin storage specialist based in Alberta, Canada, shut down on March 2014 after saying it discovered a theft of about $650,000 in bitcoins.[87] Poloniex, a digital currency exchange, reported on March 2014 that it lost bitcoins valued at around $50,000.[88] In January 2015 UK-based bitstamp, the third busiest bitcoin exchange globally, was hacked and $5 million in bitcoins were stolen.[89] February 2015 saw a Chinese exchange named BTER lose bitcoins worth nearly $2 million to hackers.[90]
A major bitcoin exchange, Bitfinex, was hacked and nearly 120,000 bitcoins (around $60m) was stolen in 2016. Bitfinex was forced to suspend its trading. The theft is the second largest bitcoin heist ever, dwarfed only by Mt. Gox theft in 2014. According to Forbes, "All of Bitfinex's customers,... will stand to lose money. The company has announced a haircut of 36.067% across the board."[91]
Thefts have raised safety concerns. Charles Hayter, founder of digital currency comparison website CryptoCompare said, "It’s a reminder of the fragility of the infrastructure in such a nascent industry."[92] According to the hearing of U.S. House of Representatives Committee on Small Business in April 2, 2014, "these vendors lack regulatory oversight, minimum capital standards and don't provide consumer protection against loss or theft."[93]
See also
References
- 1 2 3 4 Nakamoto, Satoshi (24 May 2009). "Bitcoin: A Peer-to-Peer Electronic Cash System" (PDF). Retrieved 20 December 2012.
- 1 2 3 4 5 Barber, Simon; Boyen, Xavier; Shi, Elaine & Uzun, Ersin (2012). "Bitter to Better – how to make Bitcoin a better currency" (PDF). Financial Cryptography and Data Security. Springer Publishing.
- ↑ Dean, Andrew (14 August 2014). "Online Gambling Meets Bitcoin". Retrieved 21 August 2014.
- ↑ "Block Chain Overview". bitcoin.org/. © Bitcoin Project 2009–2014 Released under the MIT license. 2009–2014. Retrieved 14 August 2014.
- 1 2 "Enabling Blockchain Innovations with Pegged Sidechains" (PDF). Blockstream. 22 October 2014. p. 3. Retrieved 9 January 2017.
- ↑ Peter Kelly-Detwiler (21 July 2016). "Mining Bitcoins Is A Surprisingly Energy-Intensive Endeavor". Forbes. Retrieved 7 January 2017.
- 1 2 Lester Coleman (25 July 2016). "As Mining Expands, Will Electricity Consumption Constrain Bitcoin?". cryptocoin news. Retrieved 7 January 2017.
- ↑ "Mining Bitcoin With Wind And Solar Power". Energy Matters. 7 November 2016. Retrieved 7 January 2017.
- ↑ Tindell, Ken (5 April 2013). "Geeks Love The Bitcoin Phenomenon Like They Loved The Internet In 1995". Business Insider.
- ↑ "Bitcoin boom benefiting TSMC: report". Taipei Times. 4 January 2014.
- ↑ Biggs, John (8 April 2013). "How To Mine Bitcoins". Techcrunch.
- ↑ Gimein, Mark (13 April 2013). "Virtual Bitcoin Mining Is a Real-World Environmental Disaster". Bloomberg Business. Bloomberg LP. Retrieved 22 April 2015.
- ↑ McCook, Hass (21 June 2014). "Under the Microscope: Economic and Environmental Costs of Bitcoin Mining". Retrieved 25 November 2016.
- ↑ "The magic of mining". The Economist. 13 January 2015. Retrieved 13 January 2015.
- 1 2 O'Brien, Matt (13 June 2015). "The scam called Bitcoin". Daily Herald. Retrieved 20 September 2016.
- ↑ Maras, Elliot (14 September 2016). "China’s Mining Dominance: Good Or Bad For Bitcoin?". Cryptocoin News. Retrieved 25 November 2016.
- 1 2 Jacob Donnelly (12 June 2016). "What is the 'Halving'? A Primer to Bitcoin's Big Mining Change". CoinDesk. Retrieved 10 January 2017.
- 1 2 Ron Dorit; Adi Shamir (2012). "Quantitative Analysis of the Full Bitcoin Transaction Graph" (PDF). Cryptology ePrint Archive. Retrieved 18 October 2012.
- 1 2 3 Jerry Brito & Andrea Castillo (2013). "Bitcoin: A Primer for Policymakers" (PDF). Mercatus Center. George Mason University. Retrieved 22 October 2013.
- 1 2 Erik Bonadonna (29 March 2013). "Bitcoin and the Double-spending Problem". Cornell University. Retrieved 22 October 2014.
- 1 2 Karame, Ghassan O.; Androulaki, Elli; Capkun, Srdjan (2012). "Two Bitcoins at the Price of One? Double-Spending Attacks on Fast Payments in Bitcoin" (PDF). International Association for Cryptologic Research. Retrieved 22 October 2014.
- 1 2 Michael J. Casey; Paul Vigna (16 June 2014). "Short-Term Fixes To Avert "51% Attack"". Money Beat. Wall Street Journal. Retrieved 30 June 2014.
- 1 2 Reid, Fergal; Harrigan, Martin (2013). "An Analysis of Anonymity in the Bitcoin System". Security and Privacy in Social Networks: 197–223.
- 1 2 3 Biryukov, Alex; Khovratovich, Dmitry; Pustogarov, Ivan (2014). "Deanonymisation of clients in Bitcoin P2P network". ACM Conference on Computer and Communications Security.
- 1 2 Houy, N. (2016). "The Bitcoin Mining Game". Ledger. 1 (0): 53–68. doi:10.5195/ledger.2016.13. Retrieved 14 January 2017.
- ↑ "How much will the transaction fee be?". Bitcoinfees.com. Retrieved 30 November 2014.
- ↑ "How porn links and Ben Bernanke snuck into Bitcoin's code". CNN Money. CNN. 2 May 2013.
- 1 2 Lavin, Tim (8 August 2013). "The SEC Shows Why Bitcoin Is Doomed". bloomberg.com. Bloomberg LP. Retrieved 20 October 2013.
- 1 2 "Bitcoins Virtual Currency: Unique Features Present Challenges for Deterring Illicit Activity" (PDF). Cyber Intelligence Section and Criminal Intelligence Section. FBI. 24 April 2012. Retrieved 2 November 2014.
- ↑ Lee, Timothy B. (21 November 2013). "Here's how Bitcoin charmed Washington". The Washington Post. Retrieved 10 October 2016.
- ↑ "Monetarists Anonymous". The Economist. The Economist Newspaper Limited. 29 September 2012. Retrieved 21 October 2013.
- ↑ Ball, James (22 March 2013). "Silk Road: the online drug marketplace that officials seem powerless to stop". theguardian.com. Guardian News and Media Limited. Retrieved 20 October 2013.
- ↑ Matthew Graham Wilson & Aaron Yelowitz (November 2014). "Characteristics of Bitcoin Users: An Analysis of Google Search Data". Social Science Research Network. Working Papers Series. SSRN 2518603
 .
. - ↑ Christin, Nicolas (2013). Traveling the Silk Road: A Measurement Analysis of a Large Anonymous Online Marketplace (PDF). Carnegie Mellon INI/CyLab. p. 8. Retrieved 22 October 2013.
we suggest to compare the estimated total volume of Silk Road transactions with the estimated total volume of transactions at all Bitcoin exchanges (including Mt.Gox, but not limited to it). The latter corresponds to the amount of money entering and leaving the Bitcoin network, and statistics for it are readily available... approximately 1,335,580 BTC were exchanged on Silk Road... approximately 29,553,384 BTC were traded in Bitcoin exchanges over the same period... The only conclusion we can draw from this comparison is that Silk Road-related trades could plausibly correspond to 4.5% to 9% of all exchange trades
- 1 2 Schweizer, Kristen (10 October 2014). "Bitcoin Payments by Pedophiles Frustrate Child Porn Fight". BloombergBusiness. Bloomberg LP. Retrieved 16 February 2015.
- ↑ Lake, Eli (17 October 2013). "Hitman Network Says It Accepts Bitcoins to Murder for Hire". The Daily Beast. The Daily Beast Company LLC. Retrieved 17 February 2015.
- ↑ Smith, Gerry (15 April 2013). "How Bitcoin Sales Of Guns Could Undermine New Rules". huffingtonpost.com. TheHuffingtonPost.com, Inc. Retrieved 20 October 2013.
- ↑ Alex, Knapp (19 January 2015), "Faking Murders And Stealing Bitcoin: Why The Silk Road Is The Strangest Crime Story Of The Decade", Forbes, retrieved 2 January 2016
- ↑ Andy Greenberg (23 October 2013). "FBI Says It's Seized $28.5 Million In Bitcoins From Ross Ulbricht, Alleged Owner Of Silk Road" (blog). Forbes.com. Retrieved 24 November 2013.
- ↑ Kelion, Leo (12 February 2014). "Five arrested in Utopia dark net marketplace crackdown". bbc.co.uk. BBC. Retrieved 13 February 2014.
- ↑ Alex Hern (3 October 2013). "Bitcoin price plummets after Silk Road closure". The Guardian. Retrieved 31 October 2014.
Digital currency loses quarter of value after arrest of Ross Ulbricht, who is accused of running online drugs marketplace
- ↑ Robert McMillan (2 October 2013). "Bitcoin Values Plummet $500M, Then Recover, After Silk Road Bust". Wired. Retrieved 31 October 2014.
- ↑ "Silk Road drug website founder Ross Ulbricht jailed". BBC News. BBC. 29 May 2015. Retrieved 30 May 2015.
- ↑ Katie Silver (31 March 2014). "Silk Road closure fails to dampen illegal drug sales online, experts say". ABC News. Retrieved 31 October 2014.
- ↑ Sophie Murray-Morris (13 February 2014). "Utopia no more: Drug marketplace seen as the next Silk Road shut down by Dutch police". The Independent. London: independent.co.uk. Retrieved 8 November 2014.
- ↑ Wakefield, Jane (7 November 2014). "Huge raid to shut down 400-plus dark net sites". bbc.com. BBC. Retrieved 8 November 2014.
- 1 2 Nate Raymond (19 December 2014). "Bitcoin backer gets two years prison for illicit transfers". Reuters. Thompson Reuters. Retrieved 20 December 2014.
- ↑ "Ross Ulbricht: Silk Road creator convicted on drugs charges". BBC. 5 February 2015. Retrieved 17 February 2015.
- ↑ Ravi Mandalia (1 December 2013). "Silk Road-like Sheep Marketplace scams users; over 39k Bitcoins worth $40 million stolen". Techie News. Retrieved 2 December 2013.
- 1 2 "Silk Road 2 loses $2.7m in bitcoins in alleged hack". BBC News. 14 February 2014. Retrieved 15 February 2014.
- ↑ "While Markets Get Seized: Pedophiles Launch a Crowdfunding Site". Retrieved 19 February 2015.
- ↑ Hopkins, Curt (7 May 2013). "If you own Bitcoin, you also own links to child porn". The Daily Dot. Retrieved 16 February 2015.
- ↑ Bradbury, Danny. "As Bitcoin slides, the Blockchain grows". IET Engineering and Technology Magazine.
- 1 2 Hajdarbegovic, Nermin (27 February 2014). "Nearly 150 strains of malware are after your bitcoins". CoinDesk. Retrieved 7 March 2014.
- ↑ Gregg Keizer (28 February 2014). "Bitcoin malware count soars as cryptocurrency value climbs". Computerworld. Retrieved 8 January 2015.
- ↑ Barski, Conrad; Wilmer, Chris (14 November 2014). Bitcoin for the Befuddled. No Starch Press. ISBN 978-1-59327-573-0.
- ↑ Zach Miners (24 February 2014). "Bitcoins, other digital currencies stolen in massive 'Pony' botnet attack". Retrieved 8 January 2015.
- ↑ Finkle, Jim (24 February 2014). "'Pony' botnet steals bitcoins, digital currencies: Trustwave". Reuters. Retrieved 7 March 2014.
- 1 2 3 "Watch out! Mac malware spread disguised as cracked versions of Angry Birds, Pixelmator and other top apps". ESET. 26 February 2014. Retrieved 20 November 2015.
- 1 2 "How Ransomware turns your computer into a bitcoin miner". The Guardian. 10 February 2014. Retrieved 7 March 2014.
- ↑ Gibbs, Samuel (21 November 2013). "US police force pay bitcoin ransom in Cryptolocker malware scam". The Guardian. Retrieved 7 March 2014.
- ↑ Usborne, Simon (15 May 2017). "Digital gold: why hackers love Bitcoin" – via The Guardian.
- ↑ Peter Coogan (17 June 2011). "Bitcoin Botnet Mining". Symantec.com. Retrieved 24 January 2012.
- ↑ Goodin, Dan (16 August 2011). "Malware mints virtual currency using victim's GPU". The Register. Retrieved 31 October 2014.
- ↑ Ryder, Greg (9 June 2013). "All About Bitcoin Mining: Road To Riches Or Fool's Gold?". Tom's hardware. Retrieved 18 September 2015.
- ↑ "Infosecurity - Researcher discovers distributed bitcoin cracking trojan malware". Infosecurity-magazine.com. 19 August 2011. Retrieved 24 January 2012.
- ↑ Lucian Constantin (1 November 2011). "Mac OS X Trojan steals processing power to produce Bitcoins: Security researchers warn that DevilRobber malware could slow down infected Mac computers". TechWorld. IDG communications. Retrieved 24 January 2012.
- ↑ "E-Sports Entertainment settles Bitcoin botnet allegations". BBC News. 20 November 2013. Retrieved 24 November 2013.
- ↑ Mohit Kumar (9 December 2013). "The Hacker News The Hacker News +1,440,833 ThAlleged Skynet Botnet creator arrested in Germany". Retrieved 8 January 2015.
- ↑ McGlaun, Shane (9 January 2014). "Yahoo malware turned Euro PCs into bitcoin miners". SlashGear. Retrieved 8 January 2015.
- ↑ Liat Clark (20 January 2014). "Microsoft stopped Tor running automatically on botnet-infected systems". Retrieved 8 January 2015.
- ↑ Hornyack, Tim (6 June 2014). "US researcher banned for mining Bitcoin using university supercomputers". PC world.com. IDG Consumer & SMB. Retrieved 13 June 2014.
- ↑ Kirk, Jeremy (28 August 2013). "Bitcoin offers privacy-as long as you don't cash out or spend it". PC World. Retrieved 31 October 2014.
- ↑ "Warning to consumers on virtual currencies" (PDF). European Banking Authority. 12 December 2013. Archived from the original (PDF) on 28 December 2013. Retrieved 23 December 2013.
- ↑ "Guidance for a Risk-Based Approach: Prepaid Cards, Mobile Payments and Internet-based Payment Services" (PDF). Guidance for a risk-based approach. Paris: Financial Action Task Force (FATF). June 2013. p. 47. Retrieved 6 March 2014.
- ↑ Lee, Dave (27 January 2014). "US makes Bitcoin exchange arrests after Silk Road closure". bbc.co.uk. BBC. Retrieved 28 January 2014.
- ↑ "UK national risk assessment of money laundering and terrorist financing" (PDF). UK HM Treasury and Home Office. Retrieved 3 May 2016.
- 1 2 "SEC charges Texas man with running Bitcoin-denominated Ponzi scheme" (Press release). US Securities and Exchange Commission. 23 July 2013. Retrieved 7 March 2014.
- ↑ Jay Adkisson (25 September 2014). "Bitcoin Savings & Trust Comes Up $40 Million Short On The Trust Part". Personal Finance. Forbes. Retrieved 13 December 2014.
- ↑ "Bitcoin: Bitcoin under pressure". The Economist. 30 November 2013. Retrieved 30 November 2013.
- ↑ Jeffries, Adrianne (19 December 2013). "How to steal Bitcoin in three easy steps". The Verge. Retrieved 17 January 2014.
- ↑ Everett, David (April 2012). "So how can you steal Bitcoins". Smartcard & Identity News. Retrieved 17 January 2014.
- ↑ Grocer, Stephen (2 July 2013). "Beware the Risks of the Bitcoin: Winklevii Outline the Downside". Moneybeat. The Wall Street Journal. Retrieved 21 October 2013.
- 1 2 Hern, Alex (9 December 2013). "Recovering stolen bitcoin: a digital wild goose chase". The Guardian. Retrieved 6 March 2014.
- ↑ Hern, Alex (8 November 2013). "Bitcoin site Inputs.io loses £1m after hackers strike twice". The Guardian. Retrieved 18 September 2015.
- ↑ "MtGox bitcoin exchange files for bankruptcy". bbc.com. BBC. 28 February 2014. Retrieved 18 April 2014.
- ↑ Ligaya, Armina (5 March 2014). "After Alberta's Flexcoin, Mt. Gox hacked, Bitcoin businesses face sting of free-wheeling ways". Financial Post. Retrieved 7 March 2014.
- ↑ Truong, Alice (6 March 2014). "Another Bitcoin exchange, another heist". Fast Company. Retrieved 7 March 2014.
- ↑ Zack Whittaker (5 January 2015). "Bitstamp exchange hacked, $5M worth of bitcoin stolen". Zdnet. CBS Interactive. Retrieved 6 January 2015.
- ↑ Millward, Steven (16 February 2015). "Nearly $2M in bitcoins feared lost after Chinese cryptocurrency exchange hack". techinasia.com. Tech In Asia. Retrieved 18 February 2015.
- ↑ Coppola, Frances (6 August 2016). "Theft And Mayhem In The Bitcoin World". Forbes. Retrieved 15 August 2016.
- ↑ Heller, Matthew (4 August 2016). "Bitfinex Hack Fuels Bitcoin Security Concerns -". CFO. Retrieved 11 January 2017.
- ↑ "Testimony of Mark T. Williams Bitcoin: Examining the Benefits and Risks for Small Business" (PDF). U.S. House of Representatives Committee on Small Business Hearing. 2 April 2014. Retrieved 10 January 2017.