Intelligent Platform Management Interface
The Intelligent Platform Management Interface (IPMI) is a set of computer interface specifications developed from a patent [US 6,367,035 B1 by Adrian White][1] for an autonomous computer subsystem that provides management and monitoring capabilities independently of the host system's CPU, firmware (BIOS or UEFI) and operating system. IPMI defines a set of interfaces used by system administrators for out-of-band management of computer systems and monitoring of their operation. For example, IPMI provides a way to manage a computer that may be powered off or otherwise unresponsive by using a network connection to the hardware rather than to an operating system or login shell.
The development of this interface was from a patent [US 6,367,035 B1 by Adrian White] the specification was led by Intel Corporation two years later and is supported by more than 200 computer systems vendors, such as Cisco, Dell, Hewlett-Packard, Intel, NEC Corporation, SuperMicro and Tyan.[2]
Functionality
Using a standardized interface and protocol allows systems-management software based on IPMI to manage multiple disparate servers. As a message-based, hardware-level interface specification, IPMI operates independently of the operating system (OS) to allow administrators to manage a system remotely in the absence of an operating system or of the system management software. Thus IPMI functions can work in any of three scenarios:
- before an OS has booted (allowing, for example, the remote monitoring or changing of BIOS settings)
- when the system is powered down
- after OS or system failure – the key characteristic of IPMI compared with in-band system management such as by remote login to the operating system using SSH
System administrators can use IPMI messaging to monitor platform status (such as system temperatures, voltages, fans, power supplies and chassis intrusion); to query inventory information; to review hardware logs of out-of-range conditions; or to perform recovery procedures such as issuing requests from a remote console through the same connections e.g. system power-down and rebooting, or configuring watchdog timers. The standard also defines an alerting mechanism for the system to send a simple network management protocol (SNMP) platform event trap (PET).
The monitored system may be powered off, but must be connected to a power source and to the monitoring medium, typically a local area network (LAN) connection. IPMI can also function after the operating system has started, and exposes management data and structures to the system management software. IPMI prescribes only the structure and format of the interfaces as a standard, while detailed implementations may vary. An implementation of IPMI version 1.5 can communicate via a direct out-of-band local area network (LAN) or serial connection or via a side-band local area network (LAN) connection to a remote client. The side-band LAN connection utilizes the board network interface controller (NIC). This solution is less expensive than a dedicated LAN connection but also has limited bandwidth.
Systems compliant with IPMI version 2.0 can also communicate via serial over LAN, whereby serial console output can be remotely viewed over the LAN. Systems implementing IPMI 2.0 typically also include KVM over IP, remote virtual media and out-of-band embedded web-server interface functionality, although strictly speaking, these lie outside of the scope of the IPMI interface standard.
DCMI (Data Center Management Interface) is a similar standard based on IPMI but designed to be more suitable for Data Center management: it uses the interfaces defined in IPMI, but minimizes the number of optional interfaces and includes power capping control, among other differences.
Side-band and out-of-band
As well as using a separate dedicated management LAN connection, IPMI also allows implementation of a so-called "side-band" management LAN connection. This connection utilizes a System Management Bus (SMBUS) interface between the BMC (Baseboard Management Controller) and the board Network Interface Controller (NIC). This solution has the advantage of reduced costs but also provides limited bandwidth – sufficient for text console redirection but not for video redirection. For example, when a remote computer is down the system administrator can access it through IPMI and utilize a text console.
This suffices for a few vital functions, such as checking the event log, accessing the BIOS setup and performing power on, power off or power cycle. However, more advanced functions, such as remote re-installation of an operating system, may require a full out-of-band management approach utilizing a dedicated LAN connection.
IPMI components
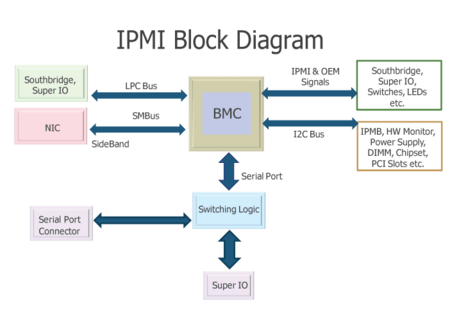
An IPMI sub-system consists of a main controller, called the baseboard management controller (BMC) and other management controllers distributed among different system modules that are referred to as satellite controllers. The satellite controllers within the same chassis connect to the BMC via the system interface called Intelligent Platform Management Bus/Bridge (IPMB) – an enhanced implementation of I²C (Inter-Integrated Circuit). The BMC connects to satellite controllers or another BMC in another chassis via the Intelligent Platform Management Controller (IPMC) bus or bridge. It may be managed with the Remote Management Control Protocol (RMCP), a specialized wire protocol defined by this specification. RMCP+ (a UDP-based protocol with stronger authentication than RMCP) is used for IPMI over LAN.
Several vendors develop and market BMC chips. A BMC utilized for embedded applications may have limited memory and require optimized firmware code for implementation of the full IPMI functionality. Highly integrated BMCs can provide complex instructions and provide the complete out-of-band functionality of a service processor. The firmware implementing the IPMI interfaces is provided by various vendors. A field replaceable unit (FRU) repository holds the inventory, such as vendor ID and manufacturer, of potentially replaceable devices. A sensor data record (SDR) repository provides the properties of the individual sensors present on the board. For example, the board may contain sensors for temperature, fan speed, and voltage.
Baseboard management controller
The baseboard management controller (BMC) is the intelligence in the IPMI architecture. It is a specialized microcontroller embedded on the motherboard of a computer, generally a server. The BMC manages the interface between system management software and platform hardware.
Different types of sensors built into the computer system report to the BMC on parameters such as temperature, cooling fan speeds, power status, operating system (OS) status, etc. The BMC monitors the sensors and can send alerts to a system administrator via the network if any of the parameters do not stay within preset limits, indicating a potential failure of the system. The administrator can also remotely communicate with the BMC to take some corrective action such as resetting or power cycling the system to get a hung OS running again. These abilities save on the total cost of ownership of a system.
Physical interfaces to the BMC include SMBus buses, an RS-232 serial console, address and data lines and an Intelligent Platform Management Bus (IPMB), that enables the BMC to accept IPMI request messages from other management controllers in the system.
A direct serial connection to the BMC is not encrypted as the connection itself is secure. Connection to the BMC over LAN may or may not use encryption depending on the security concerns of the user.
There are rising concerns about the general security regarding BMCs as a closed infrastructure.[3][4][5][6]
Current Security Status
IPMI supports the use of SSL by way of HTTPS for secure communication with certificates.
The use of default short passwords, or "cipher 0" hacks can be easily overcome with the use of a RADIUS server for Authentication, Authorization, and Accounting over SSL as is typical in a datacenter or any medium to large deployment. The user's RADIUS server can be configured to store AAA securely in an LDAP database in a secure manner using either FreeRADIUS/OpenLDAP or Microsoft Active Directory and related services.
Role-based access provides a way to respond to current and future security issues by increasing amounts of restriction for higher roles. Role-based access is supported with three roles available: Administrator, Operator and User.
Overall, the User role has read-only access of the BMC and no remote control ability such as power cycle or the ability to view or log into the main CPU on the motherboard. Therefore, any hacker with the User role has zero access to confidential information, and zero control over the system. The User role is typically used to monitor sensor readings, after an SNMP alert has been received by SNMP Network Monitoring Software.
The Operator role is used in the rare event when a system is hung, to generate an NMI crash/core dump file and reboot or power cycle the system. In such a case, the Operator will also have access to the system software to collect the crash/core dump file.
The Administrator role is used to configure the BMC on first boot during the commissioning of the system when first installed.
Therefore, the prudent best practice is to disable the use of the Operator and Administrator roles in LDAP/RADIUS, and only enable them when needed by the LDAP/RADIUS administrator. For example, in RADIUS a role can have its setting Auth-Type changed to:
Auth-Type := Reject
Doing so will prevent RAKP hash attacks from succeeding since the username will be rejected by the RADIUS server.
Table of Security Roles and Functions
Function User Operator Administrator
System Information Full Access Full Access Full Access
Chassis Locator Control View Only Full Access Full Access
FRU Reading Full Access Full Access Full Access
Sensor Readings Full Access Full Access Full Access
Event Log View View Only Full Access Full Access
Alert Settings No View Only Full Access
LDAP Settings No View Only Full Access
Mouse Mode No Full Access Full Access
Network Settings No View Only Full Access
Remote Session No View Only Full Access
SMTP Settings No View Only Full Access
SSL Settings No View Only Full Access
Users Settings No View Only Full Access
Event Action No View Only Full Access
Power Control View Only Full Access Full Access
KVM View Only Full Access Full Access
F/W Update View Only View Only Full Access
SDR Update View Only View Only Full Access
BMC Logout Full Access Full Access Full Access
Vendors have provided patches that remediate most of the vulnerabilities. The "IPMI 2.0 RAKP Authentication Remote Password Hash Retrieval" vulnerability has been addressed by the introduction of RAKP+, and RMCP has been upgraded to RMCP+. While some have theorized, no successful empirical data exists on the time to break or break-ability of RAKP+/RMCP+.
Historical Security Issues
On 2 July 2013, Rapid 7 published a guide to security penetration testing of the latest IPMI 2.0 protocol and implementations by various vendors.[7]
While some sources are even advising against using IPMI at all some of these are dated. For example, a quick check with ipmitool shows cipher zero no longer exists on the latest versions.,[8] due to security concerns related to the design and vulnerabilities of Baseboard Management Controllers (BMCs).[9][10] However, like for any other management interface, good security practices dictate the placement of the IPMI management port on a dedicated management LAN or VLAN.
Version history
The IPMI standard specification has evolved through a number of iterations:[11][12]
- v1.0 was announced on September 16, 1998: base specification
- v1.5, published on March 1, 2001: added features including IPMI over LAN, IPMI over Serial/Modem, and LAN Alerting
- v2.0, published on February 14, 2004: added features including Serial over LAN, Group Managed Systems, Enhanced Authentication, Firmware Firewall, and VLAN Support
- v2.0 revision 1.1, published on February 11, 2014: amended for errata, clarifications, and addenda, plus addition of support for IPv6 Addressing
- v2.0 revision 1.1 Errata 7, published on April 21, 2015: amended for errata, clarifications,addenda, more secure RMCP+ and RAKP+ protocols.
Implementations
- HP Integrated Lights-Out, HP's implementation of IPMI
- Dell DRAC, Dell's implementation of IPMI
- IBM Remote Supervisor Adapter, IBM's out-of-band management products, including IPMI implementations
- MegaRAC, AMI's out-of-band management product and OEM IPMI firmware used in e.g. ASUS, Tyan, Intel and Supermicro motherboards
- Avocent MergePoint Embedded Management Software, an OEM IPMI firmware used in e.g. DELL and Gigabyte motherboards
See also
- Management Component Transport Protocol (MCTP, a low-level protocol used for controlling hardware components)
- Intel Active Management Technology (AMT, Intel's out-of-band management product, as an alternative to IPMI)
- DMTF Alert Standard Format (ASF, another platform management standard)
- DMTF Desktop and mobile Architecture for System Hardware (DASH, another platform management standard)
- System Service Processor on some SPARC machines
- Wired for Management (WfM)
References
- ↑ White, Adrian Richard (2 Apr 2002), Methods and apparatus for diagnosing and correcting faults in computers by a support agent at a remote location, retrieved 2016-01-22
- ↑ "Intelligent Platform Management Interface; Adopters list". Intel. Retrieved 9 August 2014.
- ↑ "The Eavesdropping System in Your Computer - Schneier on Security". Schneier.com. 2013-01-31. Retrieved 2015-05-29.
- ↑ "InfoSec Handlers Diary Blog - IPMI: Hacking servers that are turned "off"". Isc.sans.edu. 2012-06-07. Retrieved 2015-05-29.
- ↑ Goodin, Dan (2013-08-16). "“Bloodsucking leech” puts 100,000 servers at risk of potent attacks". Arstechnica.com. Retrieved 2015-05-29.
- ↑ Anthony J. Bonkoski; Russ Bielawski; J. Alex Halderman (2013). "Illuminating the Security Issues Surrounding Lights-Out Server Management.Usenix Workshop on Offensive Technologies" (PDF). Usenix.org. Retrieved 2015-05-29.
- ↑ "Metasploit: A Penetration Tester's Guide to IPMI and BMCs". Rapid7.com. 2013-07-02. Retrieved 2013-12-05.
- ↑ "The Eavesdropping System in Your Computer". schneier.com. 2013-01-31. Retrieved 2013-12-05.
- ↑ "Authentication Bypass Vulnerability in IPMI 2.0 RAKP through the use of cipher zero". websecuritywatch.com. 2013-08-23. Retrieved 2013-12-05.
- ↑ Dan Farmer (2013-08-22). "IPMI: Freight train to hell" (PDF). fish2.com. Retrieved 2013-12-05.
- ↑ "Intelligent Platform Management Interface: What is IPMI?". Intel. Retrieved 9 August 2014.
- ↑ "Intelligent Platform Management Interface; Specifications". Intel. Retrieved 9 August 2014.
External links
- A Comparison of common IPMI Software open-source projects
- coreIPM Project - Firmware for IPMI baseboard management (open source)
- DCMI - an extension to IPMI 2.0 designed for large data centres
- GNU FreeIPMI
- Intel IPMI Home Website
- ipmiutil
- IPMItool
- OpenIPMI
- SuperMicro IPMI Client web download
- SuperMicro IPMI Client ftp download