Steganography tools
A steganography software tool allows a user to embed hidden data inside a carrier file, such as an image or video, and later extract that data.
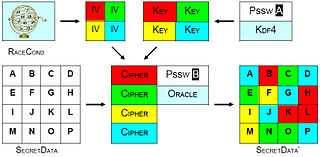
It is not necessary to conceal the message in the original file at all. Thus, it is not necessary to modify the original file and thus, it is difficult to detect nothing. If a given section is subjected to successive bitwise manipulation to generate the cyphertext, then there is no evidence in the original file to show that it is being used to encrypt a file.
Architecture
Carrier
The carrier is the signal, stream, or data file into which the hidden data is hidden by making subtle modifications. Examples include audio files, image files, documents, and executable files. In practice, the carrier should look and work the same as the original unmodified carrier, and should appear benign to anyone inspecting it.
Certain properties can raise suspicion that a file is carrying hidden data:
- If the hidden data is large relative to the carrier content, as in an empty document that is a megabyte in size.
- The use of obsolete formats or poorly-supported extensions which break commonly used tools.

It is a crypographic requirement that the carrier (e.g. photo) is original, not a copy of something publicly available (e.g., downloaded). This is because the publicly available source data could be compared against the version with a hidden message embedded.
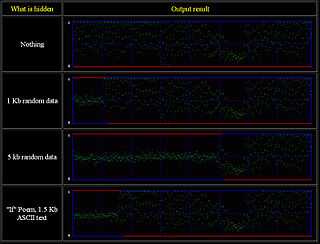
There is a weaker requirement that the embedded message not change the carrier's statistics (or other metrics) such that the presence of a message is detectable. For instance, if the least-significant-bits of the red camera-pixel channel of an image has a Gaussian distribution given a constant colored field, simple image steganography which produces a random distribution of these bits could allow discrimination of stego images from unchanged ones.
The encoded content should be compressed then encrypted. Encrypting it provides a uniform noise source which can be modulated into the carrier. It then becomes a fox-and-rabbit problem of hiders and finders (i.e. camouflage escalation) in a signal detection sense. The prey gets better at hiding, the predators at detection. The sheer volume of modern (ca 2014) and inane high-bandwidth media (e.g., youtube.com, bittorrent sources. ebay, facebook, spam, etc.) provides ample opportunity for covert communication.
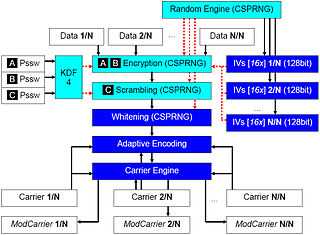
Chain
Hidden data may be split among a set of files, producing a carrier chain, which has the property that all the carriers must be available, unmodified, and processed in the correct order in order to retrieve the hidden data. This additional security feature usually is achieved by:
- using a different initialization vector for each carrier and storing it inside processed carriers -> CryptedIVn = Crypt( IVn, CryptedIVn-1 )
- using a different cryptography algorithm for each carrier and choosing it with a chain-order-dependent equiprobabilistic algorithm

Robustness and cryptography
Steganography tools aim to ensure robustness against modern forensic methods, such as statistical steganalysis. Such robustness may be achieved by a balanced mix of:
- a stream-based cryptography process;
- a data whitening process;
- an encoding process.
If the data is detected, cryptography also helps to minimize the resulting damage, since the data is not exposed, only the fact that a secret was transmitted. The sender may be forced to decrypt the data once it is discovered, but deniable encryption can be leveraged to make the decrypted data appear benign.
Strong steganography software relies on a multi-layered architecture with a deep, documented obfuscation process.
Carrier engine
The carrier engine is the core of any steganography tool. Different file formats are modified in different ways, in order to covertly insert hidden data inside them. Processing algorithms include:
- Injection (suspicious because of the content-unrelated file size increment)
- Generation (suspicious because of the traceability of the generated carriers)
- Ancillary data and metadata substitution
- LSB or adaptive substitution
- Frequency space manipulation
Tools comparison
| Program | Image files | Audio files | Video files | Document files | Other support | Notes |
| Anubis | ? | - | - | - | - | Open source |
| Steghide | ? | - | - | - | - | Open source (GNU General Public License) |
| BMPSecrets | BMP, JPG, TIFF, GIF | - | - | - | ? | Allowes to replace up to 50-60% of picture with your information |
| DarkCryptTC | BMP, JPG, TIFF, PNG, PSD, TGA, MNG | WAV | - | TXT, HTML, XML, ODT | EXE, DLL, NTFS streams | RSD mode (RNG-based random data distribution) |
| ImageSpyer G2 | BMP, TIFF | - | - | - | ? | RSD algorithm implemented, plugin for Total Commander (StegoTC G2) |
| MP3Stego | - | MP3 | - | - | - | Open source |
| OpenPuff | BMP, JPEG, PNG, TGA | MP3, WAV | 3gp, MP4, MPEG-1, MPEG-2, VOB, SWF, FLV | - | Freeware, 256-bit multi-encryption, Carrier chains, Multi-layered obfuscation | |
| OpenStego | BMP, PNG | - | - | - | - | Open source |
| Outguess-rebirth | JPG | - | - | - | - | Portable freeware Windows (based on Outguess for Linux) |
| PHP-Class StreamSteganography | PNG | - | - | - | - | - |
| Red JPEG | JPEG | - | - | - | - | XT for Total Commander, LZMA compression, PRNG-based masking and distribution |
| S-Tools | BMP, GIF | Wav | - | - | Unused floppy disk space | - |
| Steg | BMP, PNG, JPEG, GIF | - | - | - | - | Symmetric and asymmetric key cryptography, runs on Win/Linux/Mac |
| StegaMail | BMP, PNG | - | - | - | - | 56bit encryption, zLib compression |
| Steganographic Laboratory (VSL) | BMP, PNG, JPG, TIFF | - | - | - | - | Open source |
| Steganography Studio | BMP, PNG, GIF | - | - | - | - | Different hiding methods (LSB, LSB Matching, SLSB, ...), Open source |
| StegFS | - | - | - | - | Steganographic file system for Linux | - |
| StegoShare | BMP, JPEG, PNG, gif, tiff etc | - | - | stegoshare.sf.net links to stegoshare.sourceforge.net - technical & legal help | - | Open source |
See also
|
Articles
- Kharrazi, Mehdi; Sencar, Husrev T.; Memon, Nasir. "Performance study of common image steganography and steganalysis techniques" (PDF). Journal of Electronic Imaging 15 (4). doi:10.1117/1.2400672. Retrieved 28 November 2012.
- Guillermito. "Analyzing steganography software". Retrieved 28 November 2012.
- Provos, Niels; Honeyman, Peter. "Hide and Seek: An Introduction to Steganography" (PDF). IEEE Security & Privacy (IEEE Computer Society) 1 (3): 32–44. doi:10.1109/MSP.2003.10004. ISSN 1540-7993. Retrieved 28 November 2012.
- Provos, Niels. "Defending against statistical steganalysis". Proceedings of the 10th conference on USENIX Security Symposium. SSYM'01 (USENIX Association) 10: 24–37. Retrieved 28 November 2012.
- Bierbrauer, Jürgen; Fridrich, Jessica. "Constructing good covering codes for applications in Steganography" (PDF). Transactions on Data Hiding and Multimedia Security III. Lecture Notes in Computer Science (Springer Berlin Heidelberg) 4920: 1–22. doi:10.1007/978-3-540-69019-1_1. ISBN 978-3-540-69019-1. Retrieved 28 November 2012.
- Rocha, Anderson; Goldenstein, Siome, Steganography and Steganalysis: past, present, and future (PDF), First IEEE Workitorial on Vision of the Unseen (WVU'08), retrieved 28 November 2012
References
External links
- Exhaustive directory of steganography software by Dr. Neil Johnson
- Directory of network steganography software at Stegano.net