Mix network
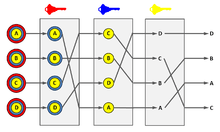
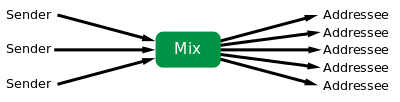
Mix networks[1] are routing protocols that create hard-to-trace communications by using a chain of proxy servers known as mixes which take in messages from multiple senders, shuffle them, and send them back out in random order to the next destination (possibly another mix node). This breaks the link between the source of the request and the destination, making it harder for eavesdroppers to trace end-to-end communications. Furthermore, mixes only know the node that it immediately received the message from, and the immediate destination to send the shuffled messages to, making the network resistant to malicious mix nodes.[2][3]
Each message is encrypted to each proxy using public key cryptography; the resulting encryption is layered like a Russian doll (except that each "doll" is of the same size) with the message as the innermost layer. Each proxy server strips off its own layer of encryption to reveal where to send the message next. If all but one of the proxy servers are compromised by the tracer, untraceability can still be achieved against some weaker adversaries.
The concept of mix networks first described by David Chaum in 1981.[4] Applications that are based on this concept include anonymous remailers (such as Mixmaster) and onion routing (including Tor).
How it works
Participant A prepares a message for delivery to participant B by appending a random value R to the message, sealing it with the addressee's public key  , appending B’s address, and then sealing the result with the mix's public key
, appending B’s address, and then sealing the result with the mix's public key  .
M opens it with his private key, now he knows B’s address, and he sends
.
M opens it with his private key, now he knows B’s address, and he sends 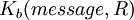 to B.
to B.
Message format

To accomplish this, the sender takes the mix’s public key ( ), and uses it to encrypt an envelope containing a random string (
), and uses it to encrypt an envelope containing a random string ( ), a nested envelope addressed to the recipient, and the email address of the recipient (B). This nested envelope is encrypted with the recipient’s public key (
), a nested envelope addressed to the recipient, and the email address of the recipient (B). This nested envelope is encrypted with the recipient’s public key ( ), and contains another random string (R0), along with the body of the message being sent. Upon receipt of the encrypted top-level envelope, the mix uses its secret key to open it. Inside, it finds the address of the recipient (B) and an encrypted message bound for B. The random string (
), and contains another random string (R0), along with the body of the message being sent. Upon receipt of the encrypted top-level envelope, the mix uses its secret key to open it. Inside, it finds the address of the recipient (B) and an encrypted message bound for B. The random string ( ) is discarded.
) is discarded.
 is needed in the message in order to prevent an attacker from guessing messages. It is assumed that the attacker can observe all incoming and outgoing messages. If the random string is not used (i.e. only
is needed in the message in order to prevent an attacker from guessing messages. It is assumed that the attacker can observe all incoming and outgoing messages. If the random string is not used (i.e. only 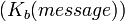 is sent to
is sent to  ) and an attacker has a good guess that the message
) and an attacker has a good guess that the message  was sent, he can test whether
was sent, he can test whether  holds, whereby he can learn the content of the message. By appending the random string
holds, whereby he can learn the content of the message. By appending the random string  the attacker is prevented from performing this kind of attack; even if he should guess the correct message (i.e.
the attacker is prevented from performing this kind of attack; even if he should guess the correct message (i.e.  is true) he won't learn if he is right since he doesn't know the secret value
is true) he won't learn if he is right since he doesn't know the secret value  . Practically,
. Practically,  functions as a salt.
functions as a salt.
Return Addresses
What is needed now is a way for B to respond to A while still keeping the identity of A secret from B.
A solution is for A to form an untraceable return address  where
where  is its own real address,
is its own real address,  is a public one-time key chosen for the current occasion only, and
is a public one-time key chosen for the current occasion only, and  is a key that will also act as a random string for purposes of sealing. Then, A can send this return address to B as part of a message sent by the techniques already described.
is a key that will also act as a random string for purposes of sealing. Then, A can send this return address to B as part of a message sent by the techniques already described.
B sends  to M, and M transforms it to
to M, and M transforms it to  .
.
This mix uses the string of bits  that it finds after decrypting the address part
that it finds after decrypting the address part  as a key to re-encrypt the message part
as a key to re-encrypt the message part  . Only the addressee, A, can decrypt the resulting output because A created both
. Only the addressee, A, can decrypt the resulting output because A created both  and
and  .
The additional key
.
The additional key  assures that the mix cannot see the content of the reply-message.
assures that the mix cannot see the content of the reply-message.
The following indicates how B uses this untraceable return address to form a response to A, via a new kind of mix:
The message from A  B:
B:

Reply message from B A:
A:

Where:  = B’s public key,
= B’s public key,  = the mix’s public key.
= the mix’s public key.
A destination can reply to a source without sacrificing source anonymity. The reply message shares all of the performance and security benefits with the anonymous messages from source to destination.
References
- ↑ Also known as "digital mixes"
- ↑ Claudio A. Ardagna et al. (2009). "Privacy Preservation over Untrusted Mobile Networks". In Bettini, Claudio et al. Privacy In Location-Based Applications: Research Issues and Emerging Trends. Springer. p. 88. ISBN 9783642035111.
- ↑ Danezis, George. "Mix-Networks with Restricted Routes". In Dingledine, Roger. Privacy Enhancing Technologies: Third International Workshop, PET 2003, Dresden, Germany, March 26-28, 2003, Revised Papers. Vol. 3. Springer. ISBN 9783540206101.
- ↑ David Chaum, Untraceable electronic mail, return addresses, and digital pseudonyms, Comm. ACM, 24, 2 (Feb. 1981); 84-90