Miller–Rabin primality test
The Miller–Rabin primality test or Rabin–Miller primality test is a primality test: an algorithm which determines whether a given number is prime, similar to the Fermat primality test and the Solovay–Strassen primality test. Its original version, due to Gary L. Miller, is deterministic, but the determinism relies on the unproven generalized Riemann hypothesis;[1] Michael O. Rabin modified it to obtain an unconditional probabilistic algorithm.[2]
Concepts
Just like the Fermat and Solovay–Strassen tests, the Miller–Rabin test relies on an equality or set of equalities that hold true for prime values, then checks whether or not they hold for a number that we want to test for primality.
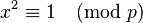
First, a lemma about square roots of unity in the finite field Z/pZ, where p is prime and p > 2. Certainly 1 and −1 always yield 1 when squared modulo p; call these trivial square roots of 1. There are no nontrivial square roots of 1 modulo p (a special case of the result that, in a field, a polynomial has no more zeroes than its degree). To show this, suppose that x is a square root of 1 modulo p. Then:
In other words, prime p divides the product (x − 1)(x + 1). By Euclid's lemma it divides one of the factors x − 1 or x + 1, implying that x is congruent to either 1 or −1 modulo p.
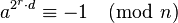
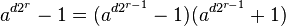
Now, let n be prime with n > 2. It follows that n − 1 is even and we can write it as 2s·d, where s and d are positive integers (d is odd). For each a in (Z/nZ)*, either
or
for some 0 ≤ r ≤ s − 1.
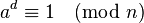
To show that one of these must be true, recall Fermat's little theorem, that for a prime number n:
By the lemma above, if we keep taking square roots of an−1, we will get either 1 or −1. If we get −1 then the second equality holds and it is done. If we never get −1, then when we have taken out every power of 2, we are left with the first equality.
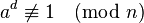
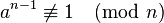
The Miller–Rabin primality test is based on the contrapositive of the above claim. That is, if we can find an a such that
and
for all 0 ≤ r ≤ s − 1, then n is not prime. We call a a witness for the compositeness of n (sometimes misleadingly called a strong witness, although it is a certain proof of this fact). Otherwise a is called a strong liar, and n is a strong probable prime to base a. The term "strong liar" refers to the case where n is composite but nevertheless the equations hold as they would for a prime.
Every odd composite n has many witnesses a, however, no simple way of generating such an a is known. The solution is to make the test probabilistic: we choose a non-zero a in Z/nZ randomly, and check whether or not it is a witness for the compositeness of n. If n is composite, most of the choices for a will be witnesses, and the test will detect n as composite with high probability. There is, nevertheless, a small chance that we are unlucky and hit an a which is a strong liar for n. We may reduce the probability of such error by repeating the test for several independently chosen a.
For testing large numbers, it is common to choose random bases a, as, a priori, we don't know the distribution of witnesses and liars among the numbers 1, 2, ..., n − 1. In particular, Arnault [3] gave a 397-digit composite number for which all bases a less than 307 are strong liars. As expected this number was reported to be prime by the Maple isprime() function, which implemented the Miller–Rabin test by checking the specific bases 2,3,5,7, and 11. However, selection of a few specific small bases can guarantee identification of composites for n less than some maximum determined by said bases. This maximum is generally quite large compared to the bases. As random bases lack such determinism for small n, specific bases are better in some circumstances.
Example
Suppose we wish to determine if n = 221 is prime. We write n − 1 = 220 as 22·55, so that we have s = 2 and d = 55. We randomly select a number a such that 0 < a < n, say a = 174. We proceed to compute:
- a20·d mod n = 17455 mod 221 = 47 ≠ 1, n − 1
- a21·d mod n = 174110 mod 221 = 220 = n − 1.
Since 220 ≡ −1 mod n, either 221 is prime, or 174 is a strong liar for 221. We try another random a, this time choosing a = 137:
- a20·d mod n = 13755 mod 221 = 188 ≠ 1, n − 1
- a21·d mod n = 137110 mod 221 = 205 ≠ n − 1.
Hence 137 is a witness for the compositeness of 221, and 174 was in fact a strong liar. Note that this tells us nothing about the factors of 221 (which are 13 and 17). However, the example with 341 in the next section shows how these calculations can sometimes produce a factor of n.
Least strong pseudoprime to base n
| n | Least SPSP | n | Least SPSP | n | Least SPSP | n | Least SPSP |
| 1 | 9 | 33 | 545 | 65 | 33 | 97 | 49 |
| 2 | 2047 | 34 | 33 | 66 | 65 | 98 | 9 |
| 3 | 121 | 35 | 9 | 67 | 33 | 99 | 25 |
| 4 | 341 | 36 | 35 | 68 | 25 | 100 | 9 |
| 5 | 781 | 37 | 9 | 69 | 35 | 101 | 25 |
| 6 | 217 | 38 | 39 | 70 | 69 | 102 | 133 |
| 7 | 25 | 39 | 133 | 71 | 9 | 103 | 51 |
| 8 | 9 | 40 | 39 | 72 | 85 | 104 | 15 |
| 9 | 91 | 41 | 21 | 73 | 9 | 105 | 451 |
| 10 | 9 | 42 | 451 | 74 | 15 | 106 | 15 |
| 11 | 133 | 43 | 21 | 75 | 91 | 107 | 9 |
| 12 | 91 | 44 | 9 | 76 | 15 | 108 | 91 |
| 13 | 85 | 45 | 481 | 77 | 39 | 109 | 9 |
| 14 | 15 | 46 | 9 | 78 | 77 | 110 | 111 |
| 15 | 1687 | 47 | 65 | 79 | 39 | 111 | 55 |
| 16 | 15 | 48 | 49 | 80 | 9 | 112 | 65 |
| 17 | 9 | 49 | 25 | 81 | 91 | 113 | 57 |
| 18 | 25 | 50 | 49 | 82 | 9 | 114 | 115 |
| 19 | 9 | 51 | 25 | 83 | 21 | 115 | 57 |
| 20 | 21 | 52 | 51 | 84 | 85 | 116 | 9 |
| 21 | 221 | 53 | 9 | 85 | 21 | 117 | 49 |
| 22 | 21 | 54 | 55 | 86 | 85 | 118 | 9 |
| 23 | 169 | 55 | 9 | 87 | 247 | 119 | 15 |
| 24 | 25 | 56 | 55 | 88 | 87 | 120 | 91 |
| 25 | 217 | 57 | 25 | 89 | 9 | 121 | 15 |
| 26 | 9 | 58 | 57 | 90 | 91 | 122 | 65 |
| 27 | 121 | 59 | 15 | 91 | 9 | 123 | 85 |
| 28 | 9 | 60 | 481 | 92 | 91 | 124 | 25 |
| 29 | 15 | 61 | 15 | 93 | 25 | 125 | 9 |
| 30 | 49 | 62 | 9 | 94 | 93 | 126 | 25 |
| 31 | 15 | 63 | 529 | 95 | 1891 | 127 | 9 |
| 32 | 25 | 64 | 9 | 96 | 95 | 128 | 49 |
Algorithm and running time
The algorithm can be written in pseudocode as follows:
Input: n > 3, an odd integer to be tested for primality;
Input: k, a parameter that determines the accuracy of the test
Output: composite if n is composite, otherwise probably prime
write n − 1 as 2s·d with d odd by factoring powers of 2 from n − 1
WitnessLoop: repeat k times:
pick a random integer a in the range [2, n − 2]
x ← ad mod n
if x = 1 or x = n − 1 then do next WitnessLoop
repeat s − 1 times:
x ← x2 mod n
if x = 1 then return composite
if x = n − 1 then do next WitnessLoop
return composite
return probably prime
Using modular exponentiation by repeated squaring, the running time of this algorithm is O(k log3n), where k is the number of different values of a that we test; thus this is an efficient, polynomial-time algorithm. FFT-based multiplication can push the running time down to O(k log2n log log n log log log n) = Õ(k log2n).
If we insert Greatest common divisor (GCD) calculations into the above algorithm, we can sometimes obtain a factor of n instead of merely determining that n is composite. In particular, if n is a probable prime base a but not a strong probable prime base a, then either GCD((ad mod n) − 1, n) or (for some r in the above range) GCD((a2r·d mod n) − 1, n) will produce a (not necessarily prime) factor of n; see page 1402 of.[4] If factoring is a goal, these GCDs can be inserted into the above algorithm at little additional computational cost.
For example, consider n = 341. We have n − 1 = 85·4. Then 285 mod 341 = 32. This tells us that n is not a strong probable prime base 2, so we know n is composite. If we take a GCD at this stage, we can get a factor of 341: GCD((285 mod 341) − 1, 341) = 31. This works because 341 is a pseudoprime base 2, but is not a strong pseudoprime base 2.
In the case that the algorithm returns "composite" because x = 1, it has also discovered that d2r is (an odd multiple of) the order of a—a fact which can (as in Shor's algorithm) be used to factorize n, since n then divides
but not either factor by itself. The reason Miller–Rabin does not yield a probabilistic factorization algorithm is that if
(i.e., n is not a pseudoprime to base a) then no such information is obtained about the period of a, and the second "return composite" is taken.
Accuracy of the test
The more bases a we test, the better the accuracy of the test. It can be shown that for any odd composite n, at least 3/4 of the bases a are witnesses for the compositeness of n.[2][5] The Miller–Rabin test is strictly stronger than the Solovay–Strassen primality test in the sense that for every composite n, the set of strong liars for n is a subset of the set of Euler liars for n, and for many n, the subset is proper. If n is composite then the Miller–Rabin primality test declares n probably prime with a probability at most 4−k. On the other hand, the Solovay–Strassen primality test declares n probably prime with a probability at most 2−k.
It is important to note that in many common applications of this algorithm, we are not interested in the error bound described above. The above error bound is the probability of a composite number being declared as a probable prime after k rounds of testing. We are often instead interested in the probability that, after passing k rounds of testing, the number being tested is actually a composite number. Formally, if we call the event of declaring n a probable prime after k rounds of Miller–Rabin Yk, and we call the event that n is composite X (and denote the event that n is prime  ), then the above bound gives us
), then the above bound gives us  , whereas we are interested in
, whereas we are interested in  . Bayes' theorem gives us a way to relate these two conditional probabilities, namely
. Bayes' theorem gives us a way to relate these two conditional probabilities, namely
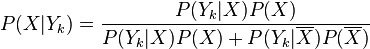 .
.
This tells us that the probability that we are often interested in is related not just to the 4−k bound above, but also probabilities related to the density of prime numbers in the region near n.
In addition, for large values of n, on average the probability that a composite number is declared probably prime is significantly smaller than 4−k. Damgård, Landrock and Pomerance[6] compute some explicit bounds and provide a method to make a reasonable selection for k for a desired error bound. Such bounds can, for example, be used to generate probable primes; however, they should not be used to verify primes with unknown origin, since in cryptographic applications an adversary might try to send you a pseudoprime in a place where a prime number is required. In such cases, only the error bound of 4−k can be relied upon.
Deterministic variants of the test
The Miller–Rabin algorithm can be made deterministic by trying all possible a below a certain limit. The problem in general is to set the limit so that the test is still reliable.
If the tested number n is composite, the strong liars a coprime to n are contained in a proper subgroup of the group (Z/nZ)*, which means that if we test all a from a set which generates (Z/nZ)*, one of them must be a witness for the compositeness of n. Assuming the truth of the generalized Riemann hypothesis (GRH), it is known that the group is generated by its elements smaller than O((log n)2), which was already noted by Miller.[1] The constant involved in the Big O notation was reduced to 2 by Eric Bach.[7] This leads to the following conditional primality testing algorithm:
Input: n > 1, an odd integer to test for primality. Output: composite if n is composite, otherwise prime write n−1 as 2s·d by factoring powers of 2 from n−1 repeat for all: if
then return composite return prime
The running time of the algorithm is Õ((log n)4) (with FFT-based multiplication). The full power of the generalized Riemann hypothesis is not needed to ensure the correctness of the test: as we deal with subgroups of even index, it suffices to assume the validity of GRH for quadratic Dirichlet characters.[5]
This algorithm is not used in practice, as it is much slower than the randomized version of the Miller–Rabin test. For theoretical purposes, it was superseded by the AKS primality test, which does not rely on unproven assumptions.
When the number n to be tested is small, trying all a < 2(ln n)2 is not necessary, as much smaller sets of potential witnesses are known to suffice. For example, Pomerance, Selfridge and Wagstaff[8] and Jaeschke[9] have verified that
- if n < 2,047, it is enough to test a = 2;
- if n < 1,373,653, it is enough to test a = 2 and 3;
- if n < 9,080,191, it is enough to test a = 31 and 73;
- if n < 25,326,001, it is enough to test a = 2, 3, and 5;
- if n < 4,759,123,141, it is enough to test a = 2, 7, and 61;
- if n < 1,122,004,669,633, it is enough to test a = 2, 13, 23, and 1662803;
- if n < 2,152,302,898,747, it is enough to test a = 2, 3, 5, 7, and 11;
- if n < 3,474,749,660,383, it is enough to test a = 2, 3, 5, 7, 11, and 13;
- if n < 341,550,071,728,321, it is enough to test a = 2, 3, 5, 7, 11, 13, and 17;
- if n < 3,825,123,056,546,413,051, it is enough to test a = 2, 3, 5, 7, 11, 13, 17, 19, and 23.
Note that Miller-Rabin pseudoprimes are called strong pseudoprimes.
Other criteria of this sort exist[10][11][12][13] and these results give very fast deterministic primality tests for numbers in the appropriate range, without any assumptions.
There is a small list of potential witnesses for every possible input size (at most n values for n-bit numbers). However, no finite set of bases is sufficient for all composite numbers. Alford, Granville, and Pomerance have shown that there exist infinitely many composite numbers n whose smallest compositeness witness is at least (ln n)1/(3ln ln ln n).[14] They also argue heuristically that the smallest number w such that every composite number below n has a compositeness witness less than w should be of order Θ(log n log log n).
Notes
- ↑ 1.0 1.1 Miller, Gary L. (1976), "Riemann's Hypothesis and Tests for Primality", Journal of Computer and System Sciences 13 (3): 300–317, doi:10.1145/800116.803773
- ↑ 2.0 2.1 Rabin, Michael O. (1980), "Probabilistic algorithm for testing primality", Journal of Number Theory 12 (1): 128–138, doi:10.1016/0022-314X(80)90084-0
- ↑ F. Arnault (August 1995). "Constructing Carmichael Numbers Which Are Strong Pseudoprimes to Several Bases". Journal of Symbolic Computation 20 (2): 151–161. doi:10.1006/jsco.1995.1042.
- ↑ Robert Baillie; Samuel S. Wagstaff, Jr. (October 1980). "Lucas Pseudoprimes". Mathematics of Computation 35 (152): 1391–1417. doi:10.1090/S0025-5718-1980-0583518-6. MR 583518.
- ↑ 5.0 5.1 Schoof, René (2004), "Four primality testing algorithms", Algorithmic Number Theory: Lattices, Number Fields, Curves and Cryptography, Cambridge University Press, ISBN 0-521-80854-5
- ↑ Damgård, I.; Landrock, P. & Pomerance, C. (1993), "Average case error estimates for the strong probable prime test", Mathematics of Computation 61 (203): 177–194, doi:10.2307/2152945
- ↑ Bach, Eric (1990), "Explicit bounds for primality testing and related problems", Mathematics of Computation 55 (191): 355–380, doi:10.2307/2008811
- ↑ Carl Pomerance; John L. Selfridge, Samuel S. Wagstaff, Jr. (July 1980). "The pseudoprimes to 25·109". Mathematics of Computation 35 (151): 1003–1026. doi:10.1090/S0025-5718-1980-0572872-7.
- ↑ Jaeschke, Gerhard (1993), "On strong pseudoprimes to several bases", Mathematics of Computation 61 (204): 915–926, doi:10.2307/2153262
- ↑ The Primes Page
- ↑ Zhang, Zhenxiang & Tang, Min (2003), "Finding strong pseudoprimes to several bases. II", Mathematics of Computation 72 (44): 2085–2097, doi:10.1090/S0025-5718-03-01545-X
- ↑ "Sloane's A014233 : Smallest odd number for which Miller-Rabin primality test on bases <= n-th prime does not reveal compositeness", The On-Line Encyclopedia of Integer Sequences. OEIS Foundation.
- ↑ SPRP Records
- ↑ Alford, W. R.; Granville, A.; Pomerance, C. (1994), "On the difficulty of finding reliable witnesses", Lecture Notes in Computer Science (Springer-Verlag) 877: 1–16, doi:10.1007/3-540-58691-1_36
External links
| The Wikibook Algorithm Implementation has a page on the topic of: Primality testing |
- Weisstein, Eric W., "Rabin-Miller Strong Pseudoprime Test", MathWorld.
- Interactive Online Implementation of the Deterministic Variant (stepping through the algorithm step-by-step)
- Applet (German)
- Miller-Rabin primality test in C#
- Miller-Rabin primality test in JavaScript using arbitrary precision arithmetic
| ||||||||||||||||||||||||||||||||||||||