Warez


Warez refers primarily to copyrighted works distributed without fees or royalties, and may be traded, in general violation of copyright law. The term generally refers to unauthorized releases by organized groups, as opposed to file sharing between friends or large groups of people with similar interest using a darknet. It usually does not refer to commercial software counterfeiting. This term was initially coined by members of the various computer underground circles, but has since become commonplace among Internet users and the mass media.
Etymology
The word warez is a leetspeak plural form of ware, short for computer software. Thus it is intended to be pronounced like the word wares, /ˈwɛərz/, but people commonly mispronounce the e, /ˈwɑrɛz/, as in the English pronunciation of Juárez.
Warez is used most commonly as a noun: "My neighbour downloaded 10 gigabytes of warez yesterday"; but has also been used as a verb: "The new Windows was warezed a month before the company officially released it". The collection of warez groups is referred to globally as the "warez scene" or more ambiguously "The Scene".
Warez distribution

Warez are often distributed outside of The Scene (a collection of warez groups) by torrents (files including tracker info, piece size, uncompressed file size, comments, and vary in size from 1 k, to 400 k.) uploaded to a popular P2P website by an associate or friend of the cracker or cracking crew. An nfo or FILE ID.DIZ is often made to promote who created the release. It is then leeched (downloaded) by users of the tracker and spread to other sharing sites using P2P, or other sources such as newsgroups. From there, it can be downloaded by millions of users all over the world. Often, one release is duplicated, renamed, then re-uploaded to different sites so that eventually, it can become impossible to trace the original file. Another increasingly popular method of distributing Warez is via one-click hosting websites.[1] In the early 1990s, warez were often traded on cassette tapes with different groups and published on bulletin boards that had a warez section.
Rise of software piracy
Piracy has been an ongoing phenomenon that started when high quality, commercially produced software was released for sale. Whether the medium was cassette tape or floppy disk, software pirates found a way to duplicate the software and spread it without the permission of the maker. Thriving pirate communities were built around the Apple II, Commodore 64, the Atari 400 and Atari 800 line, the ZX Spectrum, the Amiga, and the Atari ST, among other personal computers. Entire networks of BBSes sprang up to traffic illegal software from one user to the next. Machines like the Amiga and the Commodore 64 had an international pirate network, through which software not available on one continent would eventually make its way to every region via bulletin board systems.
It was also quite common in the 1980s to use physical floppy disks and the postal service for spreading software, in an activity known as mail trading. Prior to the sale of software that came on CD-ROM discs and after hard drives had become available, the software did not require the floppy disc to be in the drive when starting and using the program. So, a user could install it onto his/her computer and mail the disk to the next person, who could do the same. Particularly widespread in continental Europe, mail trading was even used by many of the leading cracker groups as their primary channel of interaction. Software piracy via mail trading was also the most common means for many computer hobbyists in the Eastern bloc countries to receive new Western software for their computers.

Copy-protection schemes for the early systems were designed to defeat the casual pirate, as "crackers" would typically release a pirated game to the pirate "community" the day they were earmarked for market.
A famous event in the history of software piracy policy was an open letter written by Bill Gates of Microsoft, dated February 3, 1976, in which he argued that the quality of available software would increase if software piracy was less prevalent. However, until the early 1990s, software piracy was not yet considered a serious problem by most people. In 1992, the Software Publishers Association began to battle against software piracy, with its promotional video "Don't Copy That Floppy". It and the Business Software Alliance have remained the most active anti-piracy organizations worldwide, although to compensate for extensive growth in recent years, they have gained the assistance of the Recording Industry Association of America (RIAA), the Motion Picture Association of America (MPAA), as well as American Society of Composers, Authors, and Publishers (ASCAP) and Broadcast Music Incorporated (BMI).
Today most warez files are distributed to the public via bittorrent and One-click hosting sites. Some of the most popular software companies that are being targeted are Adobe, Microsoft, Nero, Apple, DreamWorks, and Autodesk, to name a few. To reduce the spread of pirating, some companies have hired people to release "fake" torrents, which look real and are meant to be downloaded, but while downloading the individual does not realize that the company that owns the software has received his/her IP address. They will then contact his/her ISP, and further legal action may be taken by the company/ISP.[citation needed]
Causes that have accelerated its growth
In the mid-1990s, computers became more popular. This was largely attributed to Microsoft and the release of Windows 95, which made using an IBM PC compatible computer much easier for home users. Windows 95 became so popular that in developed countries nearly every middle-class household had at least one computer.[citation needed] Similar to televisions and telephones, computers became a necessity to every person in the information age. As the use of computers increased, so had software and cyber crimes.
In the mid-1990s, the average Internet user was still on dial-up, with average speed ranging between 28.8 and 33.6 kbit/s. If one wished to download a piece of software, which could run about 200 MB, the download time could be longer than one day, depending on network traffic, the Internet Service Provider, and the server. Around 1997, broadband began to gain popularity due to its greatly increased network speeds. As "large-sized file transfer" problems became less severe, warez became more widespread and began to affect large software files like animations and movies.
In the past, files were distributed by point-to-point technology: with a central uploader distributing files to downloaders. With these systems, a large number of downloaders for a popular file uses an increasingly larger amount of bandwidth. If there are too many downloads, the server can become unavailable. The opposite is true for peer-to-peer networking; the more downloaders the faster the file distribution is. With swarming technology as implemented in file sharing systems like eDonkey2000 or BitTorrent, downloaders help the uploader by picking up some of its uploading responsibilities. There are many sites with links to One-click hosting websites and other sites where one can upload files that contribute to the growing amount of warez.
Distribution via compromised FTP servers
Prior to the development of modern peer-to-peer sharing systems and home broadband service, sharing warez sometimes involved warez groups scanning the Internet for weakly secured computer systems with high-speed connections. These weakly secured systems would be compromised by exploiting the poor FTP security, creating a special directory on the server with an unassuming name to contain the illegal content.[2][3]
A common mistake of early FTP administrators was to permit a directory named /incoming that allows full read and write access by external users, but the files themselves in /incoming were hidden. By creating a directory inside /incoming, this hidden directory would then allow normal file viewing. Users of the compromised site would be directed to login and go to a location such as /incoming/data/warez to find the warez content. Messages could be left for other warez users by uploading a plain text file with the message inside.
These hackers would also use known software bugs to illicitly gain full administrative remote control over a computer, and install a hidden FTP service to host their warez. This FTP service was usually running on an unusual port number, or with a non-anonymous login name like "login: warez / Password: warez" to help prevent discovery by legitimate users. Information about this compromised system would then be distributed to a select group of people who were part of the warez scene.
It was important for warez group members to regulate who had access to these compromised FTP servers, to keep the network bandwidth usage low. A site that suddenly became very popular would be noticed by the real owners of the equipment due to their business systems having become slow or low on disk space, resulting in an investigation of system usage which inevitably results in discovery and removal of the warez, and tightening of the site security.
Automated warez distribution via IRC robots
As the ability to compromise and attain full remote control of business servers became more developed, the warez groups would hack a server and install an IRC robot on the compromised systems alongside the FTP service, or the IRC robot would provide file sharing directly by itself. This software would intelligently regulate access to the illicit data by using file queues to limit bandwidth usage, or by only running during off-hours overnight when the business owning the compromised hardware was closed for the day.[4]
In order to advertise the existence of the compromised site, the IRC software would join public IRC warez channels as a bot and post into the channel with occasional status messages every few minutes, providing information about how many people are logged in to the warez host, how many files are currently being downloaded, what the upload/download ratio is (to force users into contributing data of their own before they can download), which warez distributor is running the bot, and other status information.[5]
Note that this functionality still exists and can still be found on IRC warez channels, as an alternative to the modern and streamlined P2P distribution systems. The opportunity to find and compromise poorly secured systems on which to create an illicit warez distribution site has only increased, with the popular use of broadband service by home users who may not fully understand the security implications of having their home computer always turned on and connected to the Internet.
Types of warez
There is generally a distinction made between different sub-types of warez. The unusual spellings shown here were commonly used as directory names within a compromised server, to organize the files rather than having them all thrown together in a single random collection.
- 0-day (pronounced as zero day) - This refers to any copyrighted work that has been released the same day as the original product, or sometimes even before.[6] It is considered a mark of skill among warez distro groups to crack and distribute a program on the same day of its commercial release.
- Apps - Applications: Generally a retail version of a software package.
- Cracks - Cracked applications: A modified executable or more (usually one) and/or a library (usually one) or more and/or a patch designed to turn a trial version of a software package into the full version and/or bypass anti-piracy protections.
- Dox - Video game add-ons: These include nocds, cracks, trainers, cheat codes etc.
- EBook - E-books: These include pirated Ebooks, scanned books, scanned comics, etc.
- Games - Games: This scene concentrates on both computer based games, and video game consoles, often released as ISO or other format disk image.
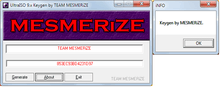
- Keygens - Keygen software are tools that replicate the registration/activation process of a genuine software product and generate the necessary keys to activate the software.
- Movies - Movies: Pirated movies, can be released while still in theaters or from CDs/DVDs/Blu-ray prior to the actual retail date.
- MP3s - MP3 audio: Pirated albums, singles, or other audio format usually obtained by ripping a CD or a radio broadcast and released in the compressed audio format MP3.
- MVids - Music videos - Can be ripped from TV, HDTV, DVDs or VCDs.
- NoCD, NoDVD, FixedExe - A file modification that allows an installed program to be run without inserting the CD or DVD into the drive.
- RIP - A game that doesn't have to be installed; any required registry entry can be included as a .reg file. RIP games can be ripped of music and/or video files, or, for video games, ROMs, thus decreasing the size of the download.[7] RIPs with nothing ripped out sometimes are referred to as DP (direct play).
- Portables - Portable applications: Similar to RIPs, but in this case they're software applications instead of video games. The point of portable software is the fact that it can be placed on removable media (or any place on the local hard drive) and doesn't need installing; usually it is compressed into one executable file, by using software like VMware ThinApp or MoleBox.
- Scripts - Scripts: These include pirated commercial scripts (such as vBulletin, Invision Power Board, etc.) coded by companies in PHP, ASP, and other languages.
- Subs - Subtitles: can be integrated in a TV-Rip or Movie.
- Serials - Refers to a collection of keys as serial numbers made available for the purpose of activating trial software, without payment.
- Templates - Templates: These include pirated commercial website templates coded by companies.
- TV-Rips - Television programs: Television shows or movies, usually with commercials edited out. Commonly released within a few hours after airing. DVD Rips of television series fall under this sub-type.
- XXX - Pornography: These can be imagesets, paysite videos or retail movies.
Movie piracy
Movie piracy was looked upon as impossible by the major studios. When dial-up was common in early and mid-1990s, movies distributed on the Internet tended to be small. The technique that was usually used to make them small was to use compression software, thus lowering the video quality significantly. At that time, the largest piracy threat was software.
However, along with the rise in broadband internet connections beginning around 1998, higher quality movies began to see widespread distribution – with the release of DeCSS, ISO images copied directly from the original DVDs were slowly becoming a feasible distribution method. Today, movie sharing has become so common that it has caused major concern amongst movie studios and their representative organizations. Because of this the MPAA is often running campaigns during movie trailers where it tries to discourage people from copying material without permission. Unlike the music industry, which has had online music stores available for several years, the movie industry only moved to online distribution in 2006, after the launch of Amazon Unbox.
Distribution of warez
File formats of warez
A CD software release can contain up to 700 megabytes of data, which presented challenges when sending over the Internet, particularly in the late 1990s when broadband was unavailable to most home consumers. These challenges apply to an even greater extent for a single-layer DVD release, which can contain up to 4.7 GB of data. The warez scene made it standard practice to split releases up into many separate pieces, called disks, using several file compression formats: (historical TAR, LZH, ACE, UHA, ARJ), ZIP, and most commonly RAR. The original purpose of these "disks" was so that each .rar file could fit on a single 1.44 MB 3½ inch floppy disk. With the growing size of games, this is no longer feasible, as hundreds of disks would need to be used. The average size of disks released by groups today are 50 megabytes or 100 megabytes, however it is common to find disks up to 200 megabytes.
This method has many advantages over sending a single large file:
- The two-layer compression could sometimes achieve almost a tenfold improvement over the original DVD/CD image. The overall file size is cut down and lessens the transfer time and bandwidth required.
- If there is a problem during the file transfer and data was corrupted, it is only necessary to resend the few corrupted RAR files instead of resending the entire large file.
- This method also allows the possibility of downloading separate ‘disks’ from different sources, as an early attempt at modern segmented downloading.
- In the case of One-click hosting websites downloading multiple files from one or several sources can significantly increase download speeds. This is because even if the source(s) provides slow download speeds on individual disks, downloading several disks simultaneously will allow the user to achieve much greater download rates.
Despite the fact that many modern ftp programs support segmented downloading, the compression via RAR, ZIP, and breaking up of files has not changed.
Releases of software titles often come in two forms. The full form is a full version of a game or application, generally released as CD or DVD-writable disk images (BIN or ISO files). A rip is a cut-down version of the title in which additions included on the legitimate DVD/CD (generally PDF manuals, help files, tutorials, and audio/video media) are omitted. In a game rip, generally all game video is removed, and the audio is compressed to MP3 or Vorbis, which must then be decoded to its original form before playing. These rips are very rare today, as most modern broadband connections can easily handle the full files, and the audio is usually already compressed by the original producer in some fashion.
Motivations and arguments
There is a growing movement, exemplified by groups like The Pirate Party and scholars at the The Mises Institute, that the very idea of intellectual property is an anathema to free society. This is in contrast to some of the more traditional open source advocates such as Lawrence Lessig, who advocate for middle ground between freedom and intellectual property. For these people the argument is not about exploiting anything; it's about the freedom to control their own property such as their computers.
Software Pirates generally exploit the international nature of the copyright issue to avoid law enforcement in specific countries.
The production and/or distribution of warez is illegal in most countries. However, it is typically overlooked in poorer third world countries with weak or non-existent protection for intellectual property. Additionally, some first world countries have loopholes in legislation that allow the warez to continue.
Legality
Warez is often a form of copyright infringement punishable as either a civil wrong or a crime. The laws and their application to warez activities may vary greatly from country to country. Generally, however, there are four elements of criminal copyright infringement: the existence of a valid copyright, that copyright was infringed, the infringement was willful and the infringement was either for commercial gain or substantial (a level often set by statute). Often public sites such as pages hosting torrent files claim that they are not breaking any laws because they are not offering the actual data but link only to other places or peers that contain the infringing material.
In addition, nearly all Web providers do not permit the hosting of warez, and will delete any site found to be hosting them.
Depending on the country, in some cases, software piracy might become legal and encouraged. As a dispute between Iran and USA over membership in WTO, and subsequent blocking of Iran's attempts at full-membership in the organization by the USA, has led Iran to encourage US software piracy. Subsequently, there has been a surge in Iranian "warez" and "crackz" websites, as unlike other countries, the Iranian laws do not forbid hosting them inside Iran. See: Iran and copyright issues
Terminology
Piracy like all other words has different shades of meaning. Some denotative, others connotative, some implying social acceptability, others pejorative. Whoever controls access to the discourse is able to pick the words with meanings that frame the reader's response. While the term 'piracy' is commonly used to describe a significant range of activities, most of which are unlawful, the relatively neutral meaning in this context is "...mak[ing] use of or reproduc[ing] the work of another without authorization".[8] Some groups (including the Free Software Foundation) object to the use of this and other words such as "theft" because they represent a partisan attempt to create a prejudice that is used to gain political ground. "Publishers often refer to prohibited copying as "piracy." In this way, they imply that illegal copying is ethically equivalent to attacking ships on the high seas, kidnapping and murdering the people on them" (FSF). The FSF advocate the use of terms like "prohibited copying" or "unauthorized copying", or "sharing information with your neighbor."
On the other hand, many self-proclaimed "software pirates" take pride in the term. Although the use of this term is controversial, it is embraced by some groups such as Pirates With Attitude.
DDL Sites or Direct Download Sites are sites that index links to locations where files can be directly downloaded to the user's computer. Many such sites link to free file hosting services, for the hosting of materials.[9] DDL sites do not directly host the material and can avoid the fees that normally accompany large file hosting.
Warez and malware
There is a common perception that warez sites represent high risk in terms of malware.[10] In addition, there are several papers showing there is indeed correlation between warez/pirate sites and malware. In particular, one study[11] shows that out of all domains the study classified as pirate, 7.1% are infected (while out of random domains only 0.4% were infected); another study[12] maintains that '"maliciousness" of the content for sites they classified as pirate (which specifically included warez sites) is the highest among all the researched site categories. Domains related to anti-copy protection tools are among the most malicious sites.[13][14] Another study specifically targeted anti-copy protection tools such as cracks and key generators. They conclude that the majority of these programs aim to infect the user's computer with one or more types of malware. The chance of the end-user being exposed to malicious code when dealing with cracked applications or games is more than 50%.[13]
See also
- Software copyright
- Copyright infringement of software
- Crack introduction
- File sharing
- Open Music Model
- List of warez groups
- .nfo - information on the text file that is almost always included in warez releases.
Notes
- ↑ Roettgers, Janko Piracy Beyond P2P: One-Click Hosters, JUN. 17, 2007, 12:00AM. Retrieved on 2010-07-06.
- ↑ Koziol, Jack (2003). Intrusion Detection with Snort. Sams Publishing. p. 72. ISBN 1-57870-281-X. (View cited page using Google Books)
- ↑ Software Piracy Exposed: How Software is Stolen and Traded Over the Internet - By Paul Craig, Ron Honick, Mark Burnett, Published by Syngress, 2005, ISBN 1-932266-98-4, Chapter 7 - The Distribution Chain, Pages 144-145 (View cited pages using Google Books)
- ↑ Koziol, Jack (2003). Intrusion Detection with Snort. Sams Publishing. p. 72. ISBN 1-57870-281-X. (View cited page using Google Books)
- ↑ Software Piracy Exposed: How Software is Stolen and Traded Over the Internet - By Paul Craig, Ron Honick, Mark Burnett, Published by Syngress, 2005, ISBN 1-932266-98-4, Chapter 7 - The Distribution Chain, Pages 145-148 (View cited pages using Google Books)
- ↑ Gehring, Verna V. (2004-08-01). "Chapter 3: Do Hackers Provide a Public Service". The Internet In Public Life. Rowman & Littlefield. p. 47. ISBN 0-7425-4234-3. "Ideally, a warez d00d tries to release "0-day warez", copies of commercial software copied, cracked, and re-released on the first day the software is available for retail sale."
- ↑ Software Piracy Exposed: How Software is Stolen and Traded Over the Internet - By Paul Craig, Ron Honick, Mark Burnett, Published by Syngress, 2005, ISBN 1-932266-98-4, Chapter 4 - Crackers, Pages 88–90 (View cited pages using Google Books)
- ↑ "The American Heritage Dictionary of the English Language: Fourth Edition "Pirate"". The American Heritage Dictionary of the English Language. Bartleby.com. Archived from the original on 2008-06-29. Retrieved 2010-02-18.
- ↑ sharky (2008-02-02). "Advanced Searching for Copyrighted Content - Part IV - 'DDL' Websites". FileShareFreak. Retrieved 2010-02-18.
- ↑ John Leyden (2005-04-21). "Warez site riddled with mobile malware". The Register.
- ↑ Alexander Moshchuk, Tanya Bragin, Steven D. Gribble, and Henry M. Levy (February 2006), A. Moshchuk, T. Bragin, S. D. Gribble, and H. M. Levy. A crawler-based study of spyware in the web., In Proceeding of the 13th Network and Distributed System Security (NDSS '06)
- ↑ Ali Ikinci (May 2007), Monkey-Spider:Detecting Malicious Web Sites, University of Mannheim, Laboratory for Dependable Distributed Systems
- ↑ 13.0 13.1 Kammerstetter, Markus, Platzer, Christian, Wondracek, Gilbert (2012). "Vanity, cracks and malware: insights into the anti-copy protection ecosystem". Proceedings of the 2012 ACM conference on Computer and communications security. CCS '12. Raleigh, North Carolina, USA: ACM. pp. 809–820. doi:10.1145/2382196.2382282. ISBN 978-1-4503-1651-4. Retrieved 2013-07-03.
- ↑ Ali Ikinci, Thorsten Holz, Felix Freiling (2008). "Monkey-Spider: Detecting Malicious Websites with Low-Interaction Honeyclients". In Proceedings of Sicherheit, Schutz und Zuverlässigkeit. Retrieved 2013-07-03.
References
- 2600 A Guide to Piracy – An article on the warez scene (ASCII plaintext and image scans from 2600: The Hacker Quarterly)
- "The Shadow Internet" – An article about modern day warez "top sites" at Wired News.
- The Darknet and the Future of Content Distribution
- BSA - Global Piracy Study - 2005 (PDF)
- BSA - Global Piracy Study - 2004 (PDF)
- Ordered Misbehavior – The Structuring of an Illegal Endeavor by Alf Rehn. A study of the illegal subculture known as the "warez scene". (PDF)
External links
| Look up warez in Wiktionary, the free dictionary. |
- Piracy Textfiles – A historical collection of documents released by warez-related individuals.
- Warez Trading and Criminal Copyright Infringement – An article on warez trading and the law, including a recap of US prosecutions under the No Electronic Theft Act.
| |||||||||||