Rate-monotonic scheduling
In computer science, rate-monotonic scheduling (RMS)[1] is a scheduling algorithm used in real-time operating systems with a static-priority scheduling class.[2] The static priorities are assigned on the basis of the cycle duration of the job: the shorter the cycle duration is, the higher is the job's priority.
These operating systems are generally preemptive and have deterministic guarantees with regard to response times. Rate monotonic analysis is used in conjunction with those systems to provide scheduling guarantees for a particular application.
Introduction
A simple version of rate-monotonic analysis assumes that threads have the following properties:
- No resource sharing (processes do not share resources, e.g. a hardware resource, a queue, or any kind of semaphore blocking or non-blocking (busy-waits))
- Deterministic deadlines are exactly equal to periods
- Static priorities (the task with the highest static priority that is runnable immediately preempts all other tasks)
- Static priorities assigned according to the rate monotonic conventions (tasks with shorter periods/deadlines are given higher priorities)
- Context switch times and other thread operations are free and have no impact on the model
It is a mathematical model that contains a calculated simulation of periods in a closed system, where round-robin and time-sharing schedulers fail to meet the scheduling needs otherwise. Rate monotonic scheduling looks at a run modeling of all threads in the system and determines how much time is needed to meet the guarantees for the set of threads in question.
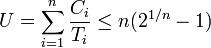
Liu & Layland (1973) proved that for a set of n periodic tasks with unique periods, a feasible schedule that will always meet deadlines exists if the CPU utilization is below a specific bound (depending on the number of tasks). The schedulability test for RMS is:
where Ci is the computation time, Ti is the release period (with deadline one period later), and n is the number of processes to be scheduled. For example, U ≤ 0.8284 for two processes. When the number of processes tends towards infinity, this expression will tend towards:
So a rough estimate is that RMS in the general case can meet all the deadlines if CPU utilization is 69.3%. The other 30.7% of the CPU can be dedicated to lower-priority non real-time tasks. It is known that a randomly generated periodic task system will meet all deadlines when the utilization is 85% or less,[3] however this fact depends on knowing the exact task statistics (periods, deadlines) which cannot be guaranteed for all task sets.
The rate monotonic priority assignment is optimal meaning that if any static priority scheduling algorithm can meet all the deadlines, then the rate monotonic algorithm can too. The deadline-monotonic scheduling algorithm is also optimal with equal periods and deadlines, in fact in this case the algorithms are identical; in addition, deadline monotonic scheduling is optimal when deadlines are less than periods.[4]
An optimal static-priority scheduling algorithm when deadlines are greater than periods is an open problem.
Avoiding priority inversion
In many practical applications, resources are shared and the unmodified RMS will be subject to priority inversion and deadlock hazards. In practice, this is solved by introducing priority inheritance. Alternative methods are to use lock free algorithms or avoid the sharing of a mutex/semaphore across threads with different priorities. This is so that resource conflicts cannot result in the first place.
Disabling of preemption
- The
OS_ENTER_CRITICAL()andOS_EXIT_CRITICAL()primitives that lock CPU interrupts in a real-time kernel (MicroC/OS-II (commonly written as uC/OS-II) kernel), - The
splx()family of primitives which nest the locking of device interrupts (FreeBSD 5.x/6.x),
Priority inheritance
Examples of priority inheritance algorithms include (from simplest to most complex):
- Linux kernel contains an implementation of this algorithm, which is a part of the in-kernel Linux real time effort to make the entire Linux kernel fully preemptive.[5]
- The basic priority inheritance protocol[6] which waits until a high priority task requests a lock held by a low-priority task, and then boosts the low priority task priority up to the high priority level until the lock is released. This method does not prevent deadlocks, but does prevent priority inversion.
- The highest locker protocol which requires off-line analysis of all task conflicts to find a "ceiling priority"
- The priority ceiling protocol[7] which is an enhancement of basic priority inheritance which assigns a "ceiling priority" to each semaphore, which is the priority of the highest job that will ever access that semaphore. A job then cannot preempt a lower priority critical section if its priority is lower than the ceiling priority for that section. This method can be sub-optimal, in that it can cause unnecessary blocking. However, it does prevent both priority inversion and deadlocks.
Priority inheritance algorithms can be characterized by two parameters. First, is the inheritance lazy (only when essential) or immediate (boost priority before there is a conflict). Second is the inheritance optimistic (boost a minimum amount) or pessimistic (boost by more than the minimum amount):
| pessimistic | optimistic | |
|---|---|---|
| immediate | OS_ENTER_CRITICAL() / OS_EXIT_CRITICAL() |
splx(), highest locker |
| lazy | priority ceiling protocol, basic priority inheritance protocol | |
In practice there is no mathematical difference (in terms of the Liu-Layland system utilization bound) between the lazy and immediate algorithms, and the immediate algorithms are more efficient to implement, and so they are the ones used by most practical systems.[citation needed]
The basic priority inheritance protocol can produce chained blocking, that is, an almost arbitrarily long delay from the time a high priority task requests a critical section, until it is served. The other protocols guarantee that at most one lower priority critical section must finish before the high priority task gets its critical section.
The priority ceiling protocol is available in the VxWorks real-time kernel but is seldom enabled.
An example of usage of basic priority inheritance is related to the "Mars Pathfinder reset bug" [8][9] which was fixed on Mars by changing the creation flags for the semaphore so as to enable the priority inheritance.
Example
| Process | Execution Time | Period |
|---|---|---|
| P1 | 1 | 8 |
| P2 | 2 | 5 |
| P3 | 2 | 10 |
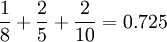
The utilization will be:
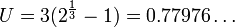
The sufficient condition for  processes, under which we can conclude that the system is schedulable is:
processes, under which we can conclude that the system is schedulable is:
Since 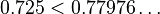 the system is surely schedulable.
the system is surely schedulable.
But remember, this condition is not a necessary one. So we cannot say that a system with higher utilization is not schedulable with this scheduling algorithm.
See also
- Deos, a time and space partitioned real-time operating system containing a working Rate Monotonic Scheduler.
- Deadline-monotonic scheduling
- Dynamic priority scheduling
- Earliest deadline first scheduling
- RTEMS, an open source real-time operating system containing a working Rate Monotonic Scheduler.
- Scheduling (computing)
References
- ↑ Liu, C. L.; Layland, J. (1973), "Scheduling algorithms for multiprogramming in a hard real-time environment", Journal of the ACM 20 (1): 46–61, doi:10.1145/321738.321743.
- ↑ Bovet, Daniel P.; Cesati, Marco, Understanding the Linux Kernel, http://oreilly.com/catalog/linuxkernel/chapter/ch10.html#85347.
- ↑ Lehoczky, J.; Sha, L.; Ding, Y. (1989), "The rate monotonic scheduling algorithm: exact characterization and average case behavior", IEEE Real-Time Systems Symposium, pp. 166–171, doi:10.1109/REAL.1989.63567.
- ↑ Leung, J. Y.; Whitehead, J. (1982), "On the complexity of fixed-priority scheduling of periodic, real-time tasks", Performance Evaluation 2 (4): 237–250, doi:10.1016/0166-5316(82)90024-4.
- ↑ "Real-Time Linux Wiki". kernel.org. 2008-03-26. Retrieved 2013-12-24.
- ↑ Lampson, B. W.; Redell, D. D. (1980), "Experience with processes and monitors in Mesa", Communications of the ACM 23 (2): 105–117, doi:10.1145/358818.358824.
- ↑ Sha, L.; Rajkumar, R.; Lehoczky, J. P. (1990), "Priority inheritance protocols: an approach to real-time synchronization", IEEE Transactions on Computers 39 (9): 1175–1185, doi:10.1109/12.57058.
- ↑ http://research.microsoft.com/~mbj/Mars_Pathfinder/
- ↑ http://anthology.spacemonkeys.ca/archives/770-Mars-Pathfinder-Reset-Bug.html
Further reading
- Joseph, M.; Pandya, P. (1986), "Finding response times in real-time systems", BCS Computer Journal 29 (5): 390–395, doi:10.1093/comjnl/29.5.390.
- Liu, Jane W.S. (2000), Real-time systems, Upper Saddle River, NJ: Prentice Hall, Chapter 6.
- Sha, Lui; Goodenough, John B. (April 1990), "Real-Time Scheduling Theory and Ada", IEEE Computer 23 (4): 53–62, doi:10.1109/2.55469
External links
- Mars Pathfinder Bug from Research @ Microsoft
- What really happened on Mars Rover Pathfinder by Mike Jones from The Risks Digest, Vol. 19, Issue 49
![\lim _{{n\rightarrow \infty }}n({\sqrt[ {n}]{2}}-1)=\ln 2\approx 0.693147\ldots](/2014-wikipedia_en_all_02_2014/I/media/3/6/2/d/362dc1a4438ec99d7387afcad4b3ab69.png)